Live from SecureWorld Boston 2022

The NetSPI team ventured from Minneapolis to Boston to attend the 2022 SecureWorld cybersecurity conference. For the first time in over two years, we saw plenty of smiling faces in the halls of the Hynes Convention Center as Boston lifted its COVID-19 mask mandate just days before the event.
While NetSPI has a growing satellite team in Boston, including managing director Nabil Hannan who is a frequent contributor to the NetSPI Executive blog, it was the first or second time to Boston for many of us. Needless to say, we took full advantage of the oysters, lobster rolls, and Italian food. Boston is truly a special city, which was made evident by the local security community members that we connected with at SecureWorld and at our post-event happy hour at Eataly.
If you skim through the SecureWorld Boston 2022 agenda you’ll quickly recognize common themes: the cybersecurity skills and diversity gap, ransomware prevention, application security, and more.
But the session descriptions can only tell you so much. Here are for four key narratives to take away from the event.
Security Awareness Training Takes Center Stage
In nearly every session we attended, security awareness training was referenced in some capacity. In many cases it was the final – and most actionable – recommendation provided.
How should you prepare for the increased cybersecurity risk amid Russia’s attack on Ukraine? Security awareness training. How can you prevent ransomware? Security awareness training. How do you secure the cloud? You guessed it… security awareness training.
One session titled, A Whole Lotta BS (Behavioral Science) About Cybersecurity, Lisa Plaggemier, Executive Director at the National Cybersecurity Alliance analyzed the results from a study that benchmarks the current state of security awareness and training.
The most shocking statistics from the report?
- Only 22% of respondents always report phishing emails to their email platform.
- 28% of respondents do not know how to report phishing emails.
- Only 12% of respondents use a password management platform, which Lisa attributed to the lack of trust within the industry due to the breaches they experienced early on.
- 48% of respondents have never heard of multi-factor authentication (MFA).
Lisa went on to explain that capability, opportunity, and motivation are necessary to get someone to form a new habit. And when it comes to cybersecurity hygiene, motivation is the hardest to achieve.
A question from the audience member validated this concept. They asked, “How can I motivate my employees to report phishing attempts more regularly?” Lisa and the audience chimed in with actionable recommendations including:
- Give people validation. Have an automated response that thanks employees for successfully identifying a phishing attempt. People want validation and a simple automated “thank you” note goes a long way.
- Gamify your social engineering assessments and reward success. An audience member implemented a program where employees receive points for properly reporting a phishing attempt. They can then cash in those points to purchase from the company store.
- Include HR in your conversations around social engineering. They will have great ideas as to what motivates people in the workplace and can help set policies for those who repeatedly fail phishing assessments.
These were timely suggestions as phishing attempts are not only more frequent, but also more successful. The State of the Phish report from Proofpoint found that 83% of organizations experienced a successful email-based phishing attack in 2021, versus 57% in 2020.
It’s no surprise that security awareness was top of mind for Boston’s security leaders at SecureWorld.
Security Decisions Should Never Be Made in a Silo
One of the most engaging sessions was called, Congratulations on CISO, Now What?. Bill Bowman, CISO at Emburse, spoke directly to the newer CISOs about how to set a solid foundation for success in the demanding role.
He began his talk with an overview of the OODA Loop: Observation, Orientation, Decision, and Action. Where are your crown jewels? How does your business make money? What exactly did you inherit? What security framework are you using? These were a few of the questions he urged CISOs to answer as they get started.
“You are the brakes that make your company go faster,” explained Bill. Yes, security may cause friction to business processes, but it also adds immense value. And it’s up to the CISO to showcase and communicate that value they bring to the table.
He went on to explain why security decisions cannot be made in a silo. “The bad guys always collaborate, and the good guys don’t,” Bill said as he urged the CISOs in the room to establish security decision making teams within their organizations.
He continued with actionable advice for building said teams, specifically a policy review board and an infosec committee. Bill suggested that the policy review board should consist of thought leaders with clout and legal teams. While infosec teams should consist of not only who the CISO reports to, but also the technical security engineering team: those in charge of penetration testing, vulnerability scanning, bug bounty programs. These are people who understand where your security program is at and how to improve it, tactically.
Bill ended the session with insights around security awareness and the need to understand what types of security content people are interested in.
Delivering content that truly interests them, whether that’s through monthly meetings or an internal newsletter, allows you to seamlessly connect your security program to your employees. Plus, he dug deeper into how to establish metrics that matter, including vulnerability management metrics, and the need to prepare for a crisis early on and establish relationships with law enforcement contacts in the event of a breach. If you ever get a chance to hear Bill speak, don’t miss it!
Cloud Security is a Shared Responsibility
One narrative that resonated across all of the cloud security sessions was the Shared Responsibility Model, the concept that cloud security is both the responsibility of the cloud providers, AWS, Azure, Google Cloud Platform (GCP) and the organizations who use the technology.
At NetSPI, we practice this through our cloud penetration testing services. We help our customers identify cloud platform misconfigurations and fix vulnerabilities on the end-user side. Every organization must take responsibility for their own cloud security.
In an early panel, speakers discussed how the shift to fully remote and hybrid workforce models have increased the urgency to improve cloud security. When the moderator asked the audience, “Who has a formal work-from-home policy in place for their employees?” Shockingly, only a few hands were raised out of the crowd of at least 50.
They continued to speak about the long-term technological impact of COVID-19, how expectations have changed, and why cloud services have become much more valuable today. Their final words of wisdom? If you’re migrating to the cloud, take the time to do things properly the first time. Silo your technologies, work with your data scientists, and leverage cloud pentesting and bug bounty programs to find security flaws before bad actors do.
It’s Necessary to Pause Before Reacting to a Crisis
With all eyes on Ukraine and the threat of cyberwarfare looming across the globe, panelists from an afternoon keynote session, Live from Ukraine: How Does Your Crisis Management Playbook Stack up During a Real-World Conflict?, explain why organizations need to pause before reacting to a crisis situation.
Why? Empathy.
DataRobot CISO Andy Smeaton joined the panel live from Poland where he was helping Ukrainians find safety and aid in humanitarian efforts. He was joined by Esmond Kane, CISO at Steward Health Care, Selva Vinothe Mahimaidas, CISO at Houghton Mifflin Harcourt, and Eric Gauthier VP of Infrastructure & Security at Emsi Burning Glass.

“Plans are essentially useless, but planning is essential,” quoted one of the panelists. They discussed tabletop exercises and provided some recommendations on how to run an effective session and what to do when a real crisis, such as a breach, happens. Advice included:
- Review your incident response plan. Refresh your understanding of the content and revisit the corresponding notes from the last tabletop for hidden gems and key insights.
- Tabletop exercises should focus on outcomes.
- Start small. Book an hour to start and grow and improve the sessions from there.
- Use what you have sitting in front of you. Evaluate the security controls you already have and understand how to use them to your advantage versus buying new technologies to fill a gap.
- Ask yourself, is this your crisis?
- Include security and IT teams in the planning phase. Let them participate and express judgement. It’s important to have a critical view of your playbook.
- Take a deep breath. The more you project calmness and control, the better you will respond.
- Be realistic. Smaller security teams will take more time, resources, and money compared to larger teams.
It’s challenging to prioritize planning for something that might not happen, but it’s vitally important. The most difficult factor of crisis planning and response according to the panelists? The human factor. There’s no playbook for how to deal with your emotions.
The panelists went on to explain that CISOs must practice empathy as employees grapple with the impact of the war. Humans are imperfect and they will fall victim to misinformation and phishing attempts. It’s up to security leaders to hit pause, reflect, and lean on their team to make thoughtful decisions together to not only protect their business and their job, but also their people.
A Successful Happy Hour with Team NetSPI
Following the event on Wednesday, NetSPI hosted a happy hour at Eataly just next door to the convention center. We continued the conversations around security leadership, increasing threats, penetration testing services, and more while we enjoyed themed cocktails (appropriately named “NetSPIked” and “Netgroni”) and delicious Italian bites.
Check out this recap of the event:
Want to connect with us at a security event or NetSPI happy hour? Visit our events page to find out where NetSPI is heading next!
Explore More Blog Posts

LiteLLM Supply Chain Compromise
A supply chain attack compromised LiteLLM versions 1.82.7 and 1.82.8 on PyPI, exfiltrating credentials and secrets to an attacker-controlled server.
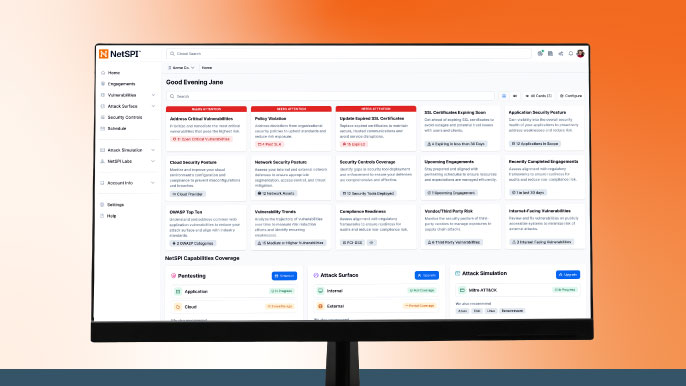
Meet NetSPI’s Modern Pentesting Experience: Use Case-Driven, AI-Accelerated
The new NetSPI experience represents the next evolution of pentesting—smarter, faster, and designed for scale.
Forrester Recognizes NetSPI in Proactive Security Landscape Report
NetSPI has been recognized among Notable Vendors in the Forrester Proactive Security Platforms Landscape, Q1 2026. Learn how we unify ASM, VRM, and pentesting.