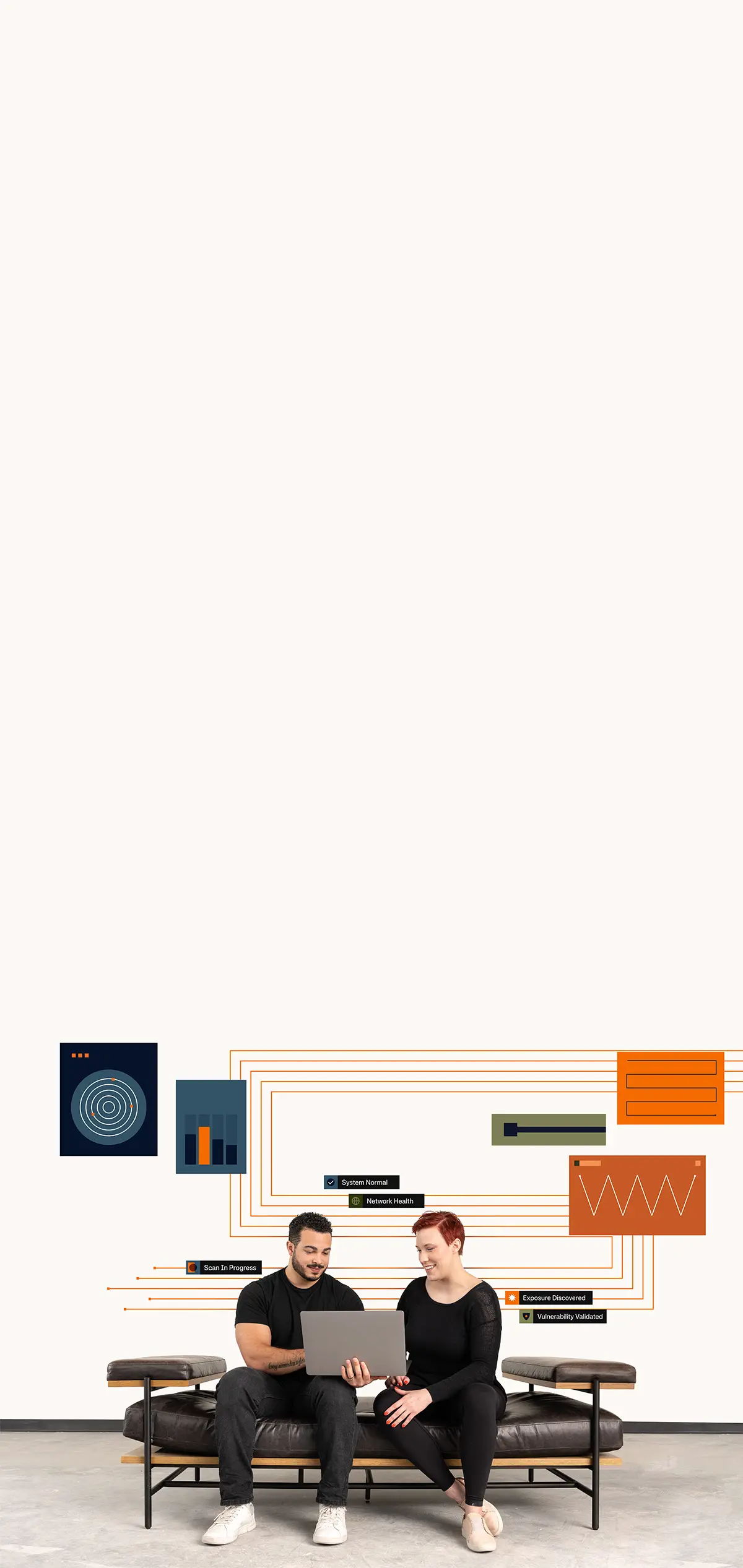
Detective Controls Testing
Measure the efficacy of your detective security controls against real-world attack simulations in your environment.
Focused Attack Simulation Packs
Understanding how an attacker views your environment and how ready your organization is to defend it is critical. NetSPI Detective Controls Testing validates that your security tools are operating effectively across endpoint security solutions, network security solutions, SIEMs, and MSSPs. Our team of experts help identify critical gaps, including misconfigurations and missed detections, and provide focused testing (simulation packs) to fit your environment.
“”


 Integrations & API
Integrations & API  MacOS
MacOS  Ransomware
Ransomware  ESXi
ESXi 
 Data Sheet
Data Sheet  Simulation Packs
Simulation Packs  Solution Brief
Solution Brief  Platform Integrations
Platform Integrations  Attack Surface Visibility
Attack Surface Visibility  Vulnerability Prioritization
Vulnerability Prioritization