NetSPI Platform
Vulnerability
Prioritization
NetSPI vulnerability prioritization cuts through the noise to surface the risks that matter most, so teams can fix faster and reduce real-world exposure.
NetSPI Prioritization Methodology
NetSPI goes beyond standard risk scoring by integrating the human intelligence of our penetration testers. Our security experts assess and prioritize risk based on a deep understanding of the client’s business, technical environment, specific needs, and industry standards (CVSS, EPSS, KEV).
-
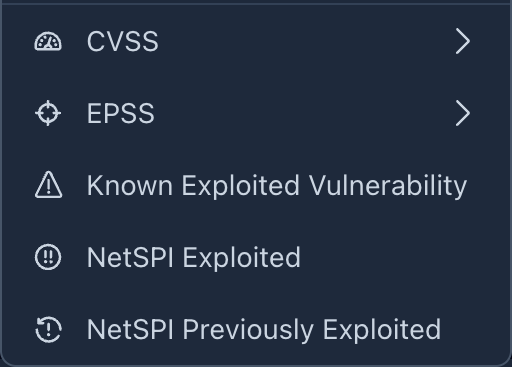
CVSS
Common Vulnerability Scoring System
-
KEV
Known Exploited Vulnerabilities
-
EPSS
Exploit Prediction Scoring System
Context-Driven Insights
Together, these three scores give your team the full picture: how severe a vulnerability is, how likely it is to be exploited, and whether it's already being used against organizations like yours. NetSPI puts these in context alongside our own exploitation data, so you're never prioritizing in the dark.
-
1
NetSPI Previously Exploited
-
2
NetSPI Exploited
-
3
Severity Indicator
1 ) NetSPI Previously Exploited
Every vulnerability in your report is tagged with a NetSPI Previously Exploited indicator when our consultants have successfully exploited that vulnerability in a real client environment. When you see that indicator, you know it’s not just a possible risk, it's proven.
2 ) NetSPI Exploited
The NetSPI Exploited indicator means our consultants didn’t just find a vulnerability. They exploited it. During your engagement, one or more instances of this vulnerability were actively leveraged by our team, proving that an attacker could do the same in your environment today.
3 ) Severity Indicator
NetSPI severity ratings are expert-curated and grounded in real-world engagements, reflecting how vulnerabilities actually behave, not just how they score. Customize severity to match your business and risk tolerance so you can prioritize what matters most.
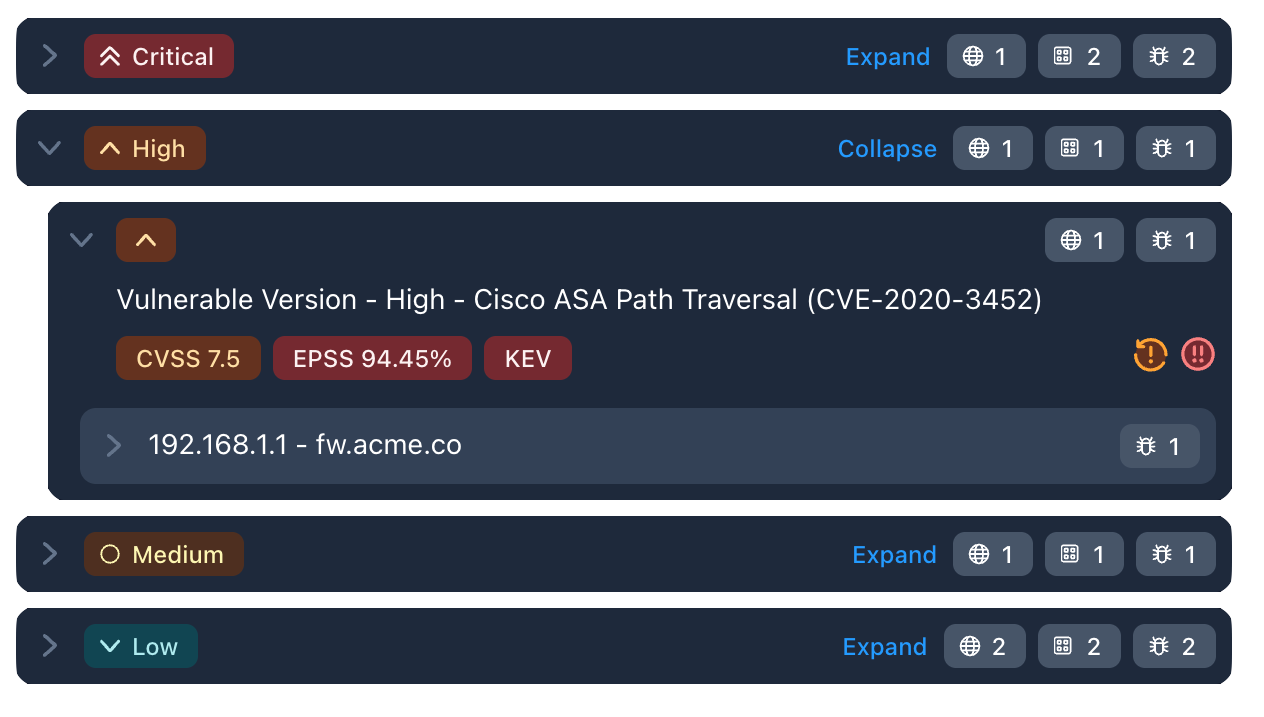
NetSPI Platform Vulnerability Tree
Organize by asset, engagement, severity, or vulnerability
- Get answers to critical security questions faster, aligned to your priorities
- Spend less time sorting and more time fixing what matters most
- Accelerate prioritization and remediation across the attack surface

Pentesting Solution
Testing and Reporting
Other Vendors
Program and findings management


Program and findings management


Remediation testing


Remediation testing


Trend analysis and real-time dashboards


Trend analysis and real-time dashboards


PDF reports


PDF reports


Attack Surface Visibility
Other Vendors
Asset inventory and deduplication


Asset inventory and deduplication


External asset discovery scans

External asset discovery scans

AWS security configuration scans

AWS security configuration scans

Dark web monitoring

Dark web monitoring

Vulnerability Prioritization
Other Vendors
Based on exposure, impact, exploitability
(CVE, CVSS, CPE, EPSS, KEV)


Based on exposure, impact, exploitability
(CVE, CVSS, CPE, EPSS, KEV)


NetSPI Previously Exploited and Exploited

NetSPI Previously Exploited and Exploited

Attack Simulation
Other Vendors
Self-service playbooks & agent execution

Self-service playbooks & agent execution

Automated detection verification

Automated detection verification

Vendor coverage comparison

Vendor coverage comparison

Integrations
Other Vendors
Open API


Open API


Assets, IAM, Detective Controls & More

Assets, IAM, Detective Controls & More

“”
Guidance From Top Experts
Collaborate in real time with our 350 in-house pentesters that you can trust to deliver consistent, quality manual pentesting results.
Accelerated Remediation
Live, interactive vulnerability reports make the path to remediation clear and easy. Integrate with your ticketing systems and tools to streamline the remediation process.
Improve Asset & Data Fidelity
Contextualize your pentesting data with high fidelity, manually validated findings, and tracking for the state of remediation efforts across all your vulnerabilities.
 Solution Brief
Solution Brief  Data Sheet
Data Sheet  Case Study
Case Study