Expert Cloud Pentesting for Today’s Threat Landscape
NetSPI cloud experts perform manual and automated pentests with a blend of commercial, open source, and proprietary tools to ensure no stone is left unturned. Our specialized cloud experts probe your AWS, Azure, or GCP infrastructures from the inside out from the perspective of both anonymous and authenticated users. These proven cloud testing methodologies find issues in your identity and access management policies, as well as misconfigurations that turn into high risk vulnerabilities across your attack surface.
OWASP Top 10 Coverage
Industry Leading Cloud Penetration Testing
The NetSPI Platform enables real-time collaboration with our cloud pentesters who have an in-depth understanding of your environment and objectives. They are supported by advanced certifications such as OSCP, OSCE, GXPN, GPEN, GWAPT, CISSP, CEH, and CREST. The result is testing that meets enterprise and regulatory standards while delivering confidence that critical exposures are identified, validated, and prioritized.
“”
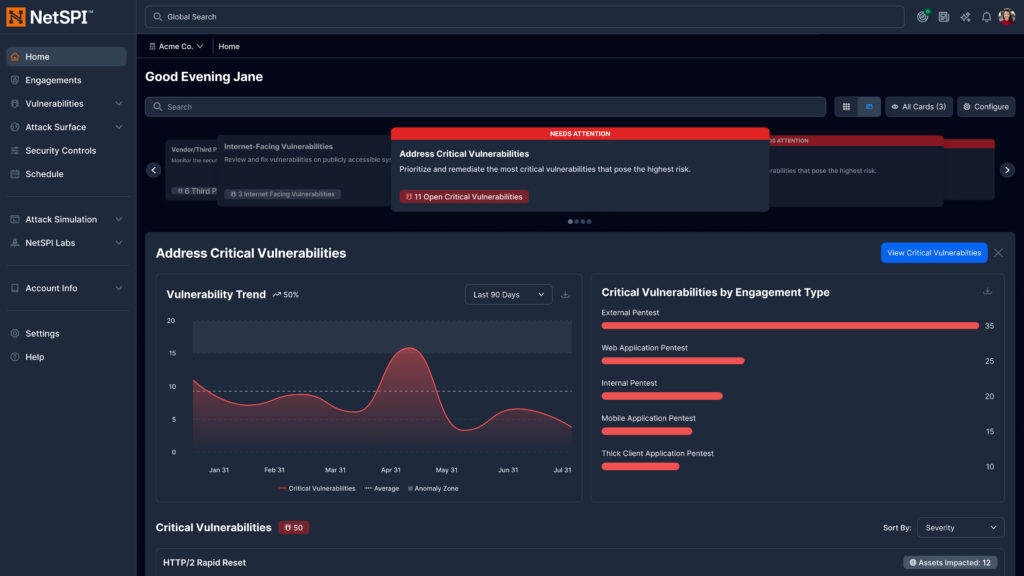
The New NetSPI Platform Experience
- Get answers to critical security questions faster, aligned to role and priorities
- Manage integrations, scans, and agents in one centralized workflow
- Accelerate detection, prioritization, and remediation across the attack surface
- Clearly demonstrate security outcomes to technical and executive stakeholders
“”
Cloud Pentesting Methodology
NetSPI pentests your cloud infrastructure wherever it is hosted. We follow manual and automated penetration testing processes that use commercial, open source, and proprietary cloud pentesting tools to evaluate your AWS, Azure or GCP infrastructure from the perspective of anonymous and authenticated users.

Configuration Review
Our expert cloud pentesters evaluate the configurations of your AWS, Azure or GCP services and the identity and access management policies applied to those services. Misconfigurations can lead to significant security impacts in AWS, Azure or Google Cloud Platform environments.

External Cloud Pentesting
External cloud security testing solutions include vulnerability scans and manual pentesting probes of your AWS, Azure or GCP infrastructure to uncover issues in public-facing services. This includes web and network-related security issues.

Internal Network Pentesting
Internal network layer testing of virtual machines and services enables NetSPI to emulate an attacker that has gained a foothold on a virtual network.

Steven Jatnieks
Chief Technology Officer, Safari

Jeremy Maxwell
Chief Security Officer, Veradigm
Featured Resources

Elevating Privileges with Azure Site Recovery Services
Discover how NetSPI uncovered and reported a Microsoft-managed Azure Site Recovery service vulnerability and how the finding was remediated.

Azure Deployment Scripts: Assuming User-Assigned Managed Identities
Learn how to use Deployment Scripts to complete faster privilege escalation with Azure User-Assigned Managed Identities.

Extracting Sensitive Information from the Azure Batch Service
Added power and scalability of Batch Service helps users run workloads faster, but misconfigurations can expose sensitive data.
You Deserve The NetSPI Advantage
 Human-Led
Human-Led
- 350+ pentesters
- Employed, not outsourced
- Wide domain expertise
 AI-Accelerated
AI-Accelerated
- Consistent quality
- Deep visibility
- Transparent results
 Modern Pentesting
Modern Pentesting
- Use case driven
- Friction-free
- Built for today’s threats