Q&A with Michelle Eggers: An Inside Look at the SANS ICS Security Summit 2023

Most people rarely think about the systems that keep our world running. But every once in a while, it’s worth it to pause and reflect on the critical infrastructure that makes our society run smoothly. In this case, we‘re talking about the security of industrial control systems (ICS).
When daily activities go as planned, everyone carries on, but if things go awry, what can be a bad day for IT applications can mean taking an entire system offline in the ICS arena. In some cases, this can be hazardous to human safety and potentially cause environmental disasters. In fact, there’s an entire conference dedicated to ICS — and we’ve got the inside scoop.
NetSPI Security Consultant Michelle Eggers earned a scholarship from Dragos and SANS to attend the ICS Security Summit & Training 2023. The summit is a deep dive into the field of ICS security, creating the space to share ideas, methods, and techniques for safeguarding critical infrastructure. We caught up with Michelle to share her experience and recap educational takeaways, memorable moments, and why ICS security is an important field of focus.
Q&A with Michelle Eggers on ICS Security Summit & Training 2023
1. How would you summarize your experience at the SANS ICS Security Summit 2023?
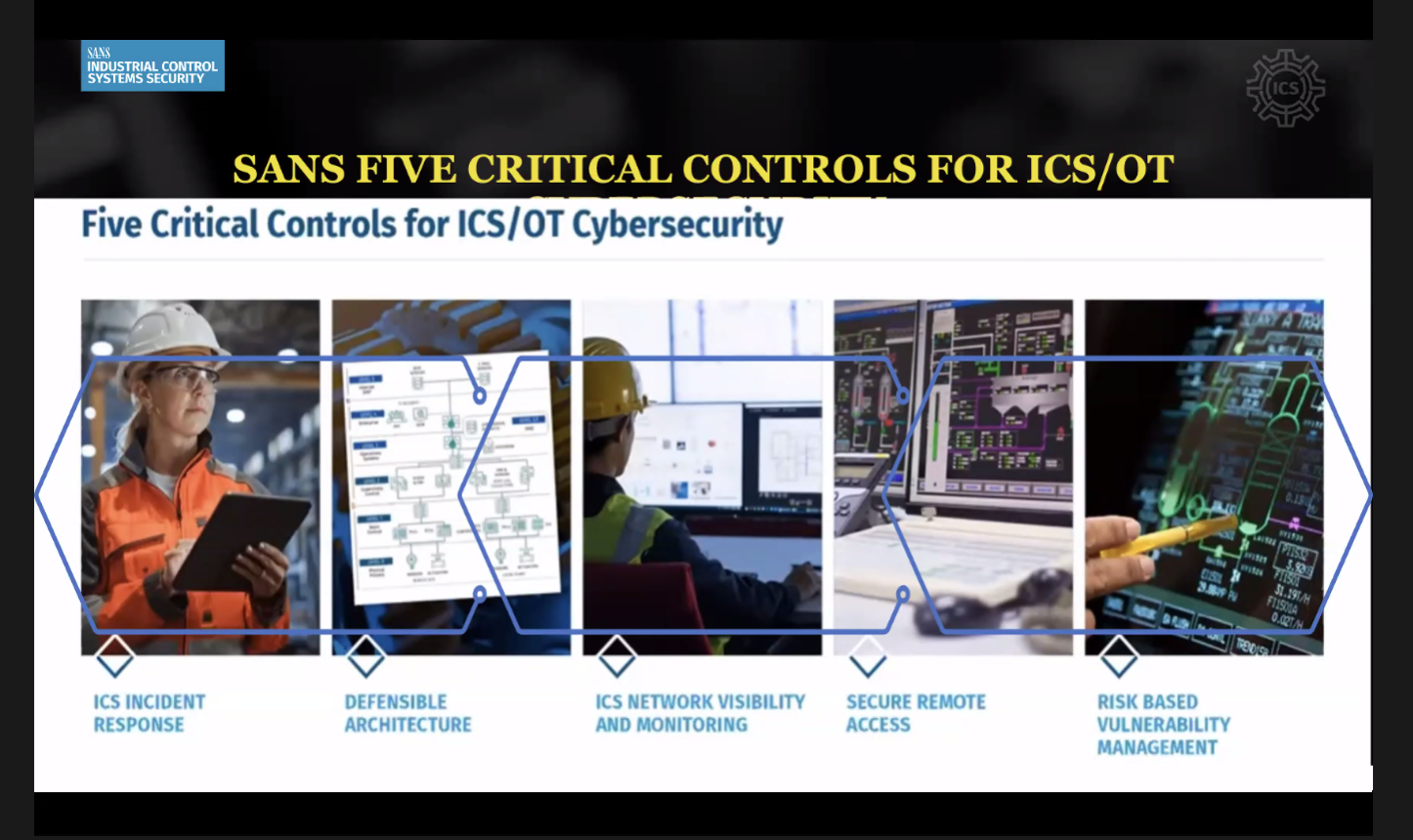
The SANS ICS Summit was a phenomenal opportunity to undergo a crash-course into many foundational aspects of Operational Technology (OT) and the current trends surrounding the technologies used to support critical infrastructure worldwide.
I had the opportunity to sit in on the beta rollout of the new SANS ICS 310 course and took away many valuable insights, such as a comparative analysis on the ways in which ICS and IT security concerns are similar, and the areas in which they differ dramatically.
Each talk during the summit provided relevant, actionable information for ICS asset owners and operators with recommendations for navigating the current threat landscape. As a note, ransomware is by far the biggest concern facing the field at this time. In short, the conference presented zero filler and instead focused on rich information directly applicable to real-world scenarios.
2. What did you find most interesting in terms of tools used to secure ICS?
Tooling wise, testing OT systems can be very similar to other types of penetration testing. The differences lie within the implementation. For example, Industrial Control Systems are often built on decades-old legacy hardware that may not be equipped to manage an active scan. In fact, something like a Nessus scan could easily knock out an entire system.
While this situation may be a bad day for IT applications, in the ICS arena, taking a system offline can be hazardous to human safety and in extreme situations could even lead to an environmental disaster or loss of life.
Cybersecurity for IT systems is built upon the CIA Triad model: Confidentiality, Integrity, and Availability. When working with operational technology, confidentiality is not the top priority; safety and availability instead play a much more crucial role. The impact goes beyond the potential loss or compromise of data or dollars and extends to potentially catastrophic effects in real-time, physical scenarios.
3. How did you get introduced to ICS security?
I first encountered the topic of ICS Security when I began my initial cybersecurity educational journey. It was not a large focus area but was mentioned in passing for general awareness purposes. I recall hearing at the time that air-gapped systems protect much of operational technology, but during the summit I came to understand that many OT systems are in fact networked and if there is an “air-gap” in place it is often a logical and not a physical separation, which as we know presents an opportunity for attacks that target bypassing security controls such as a misconfigured firewall.
4. What makes you passionate about ICS security?
Most people across the globe rely daily upon manufactured products or foods, critical infrastructure services (like healthcare), or utilities such as water or power to survive. The only way to escape the need for what OT provides us would be to live completely off grid, growing our own food, creating our own medicine, and so on.
While this sounds ideal to some, the reality is very few people are actually living this way in industrialized countries. Industrial Control Systems are a crucial component of our daily lives whether we acknowledge it or not, and keeping these systems secure is of the utmost importance.
5. Do you have a vision for how you could merge your pentesting skillset with operational technology (OT)?
Ah, the dream! I would love to merge my existing interests in OSINT, Social Engineering, Physical Pentesting, and my current work in Web Application Penetration Testing with OT Pentesting into a well-rounded Red Team role that would assist organizations in securing their most vital assets in a multi-tiered and comprehensive approach.
As far as OT testing branching out from Web App testing, many industrial control systems have some form of network connectivity that incorporates human-machine interfaces, and these can often present very similar vulnerabilities to IT systems regarding the authentication process. If forged remote authentication can be achieved to a workstation in control of a real-world, physical process you’ve got a very serious problem at hand.
6. What tips do you have for security professionals looking to learn more about ICS security?
Resources abound. Everything from YouTube to a basic browser search can provide a solid starting point for a better understanding of Operational Technology. I would recommend reading about the Colonial Pipeline cyberattack, studying up on Stuxnet and the Ukraine power grid attacks, and investigating any other infrastructure attacks of interest to gain a general idea of the OT landscape and what’s at stake.

While at the conference I also had the opportunity to chat with Robert M. Lee, SANS ICS Fellow, who has put together a wonderful blog providing a list of resources for those interested in growing their knowledge base on ICS Cybersecurity, “A Collection of Resources for Getting Started in ICS/SCADA Cybersecurity.”
In addition, Dean Parsons has also released several free PDF resources on the subject, entitled “ICS Cybersecurity Field Manual” Volumes 1-3. These will also be available soon in a consolidated hardcopy edition as well. I managed to snag a signed first edition copy of his book at the Summit and it’s an excellent read, I wholeheartedly recommend adding it to any cybersecurity resource collection.
If ICS security piques your interest, then you’ve got some reading to do! Connect with Michelle Eggers on LinkedIn for more OT insights and learn about NetSPI’s OT-centric offensive security services here.
Explore More Blog Posts

Phishing with Misfortune Cookies
Phishing is about creativity. The less likely your target is to think about a link being potentially malicious, the more likely you are to have success. Read how our creative Social Engineering experts ruined free cookies in the break room.

CVE-2026-9082 Drupal Core PostgreSQL SQL Injection Overview and Takeaways
A critical vulnerability in Drupal Core, tracked as CVE-2026-9082, affects Drupal deployments using a PostgreSQL database. The issue allows unauthenticated attackers to perform arbitrary SQL queries via crafted JSON:API or search queries. Successful exploitation may result in full database compromise or remote code execution.

Emulating & Exploiting UEFI: Unveiling Vulnerabilities in Firmware Security
Explore the intricacies of UEFI security with exploration into emulation, dynamic analysis, and the LogoFail vulnerability. Learn how subtle input manipulations can expose critical firmware weaknesses.