Application Penetration Testing
Our application pen testing services identify, validate, and prioritize security vulnerabilities in your web apps, mobile apps, thick client apps, and virtual applications.

Proactive Application Security
Your most important apps deserve expert application security penetration testing. NetSPI’s dynamic application security testing experts leverage highly specialized cybersecurity testing tools, custom application pen testing setups, and ethical hacking techniques to find and exploit application security gaps, and prioritize the most important security vulnerabilities for you.

Web Application Penetration Testing
NetSPI identifies security vulnerabilities in the network, system, and layers of a web app that allow us to escalate user privilege, manipulate data, and gain access to restricted functionality or data. We manually verify all exploitable and significant vulnerabilities.
During our web application penetration testing service, NetSPI evaluates your web app for security vulnerabilities, and provides actionable guidance for remediating the vulnerabilities and improving your organization’s security risk posture.
NetSPI identifies vulnerabilities in your mobile app infrastructure that make your organization susceptible to an external or internal cybersecurity threat.
NetSPI pentests on Android and/or iOS for vulnerabilities. We evaluate the target app from the perspective of both anonymous and authenticated users and manually pentest for security controls in four essential areas: file system, memory, network communications, and GUI.

Thick Client Application Penetration Testing
NetSPI uses multi-vector pentesting to identify vulnerabilities within interactive and headless thick client apps deployed on Windows, Linux/Unix, and macOS. NetSPI’s approach to thick app penetration testing includes reviewing server-side and client-side controls, data communication paths, data storage, and authorization/authentication best practices.
For apps that are hosted, or use cloud services, NetSPI has an additional set of penetration tests to ensure the deployment and cloud environments are secure.

API Penetration Testing
API Penetration Testing is critical for a modern security program. It helps security and development teams inventory their APIs, evaluate them for security vulnerabilities, and provide actionable recommendations for focused improvement to a company’s security posture. Our team of offensive security specialists can help you test a specific API, or incorporate API security into your overall development process.
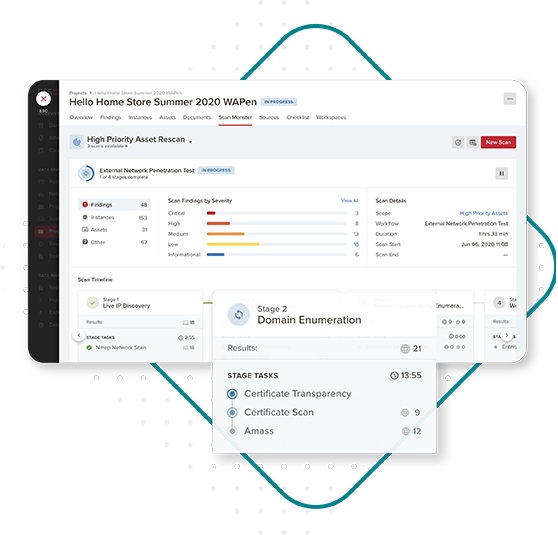
Human-Driven Automated Pentesting (H-DAP)
H-DAP uses industry standard DAST scanning tools paired with targeted manual penetration testing, allowing companies to rapidly test with confidence and improve coverage across a portfolio of web applications.
-
StreamlineAutomated scanning establishes a vulnerability baseline faster. Manual validation and triaging provide near-zero false positives, delivering actionable information from noise.
-
SecureHumans perform targeted manual penetration testing to discover findings that scanners simply can’t. Plus, tap into our team for prioritization and remediation support.
-
ScaleExpand coverage by testing more of your web application portfolio, instead of only high-risk apps.
Virtual Application Penetration Testing
During virtual app penetration testing, NetSPI identifies the risks specific to applications published through virtualization platforms and uses traditional penetration testing to help ensure that your company is protecting its attack surface while adapting to evolving business needs.
During virtual application breakout assessments, NetSPI identifies cybersecurity vulnerabilities that provide unauthorized access to the operating system through apps published via virtualization platforms such as Citrix and VMware.
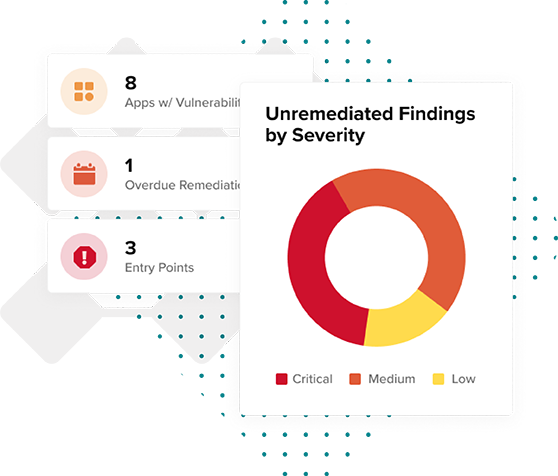
AppSec as a Service
NetSPI’s AppSec as a Service helps our clients manage multiple areas of their application security program. By partnering with NetSPI, you can free up your team members’ time to focus on more strategic initiatives, while NetSPI provides support of day-to-day application security operations.
This appsec service combines the power of technology through our Resolve™ vulnerability management and orchestration platform and our leading application security consulting services to ensure you can build and manage a world-class app security program. Partner with NetSPI to drive your application security program forward and meet your cybersecurity objectives.

Application Security Penetration Testing Resources
Your application security program has room for improvement. Get this 6-part whitepaper and get started on your journey to mature your application security program and reduce risk.
A cybersecurity program is as individual as an organization. If you’re about to embark on a security journey, these activities will set you on the right path.
A successful application security program requires collaboration between people, processes, and technology. Watch this on-demand webinar shown at Black Hat to get started.
