Internal Network Pentesting
Internal threats and cloud-based vulnerabilities create security risks when they extend into hosted environments with ties to internal networks. NetSPI’s internal network penetration testing simulates the actions of a skilled attacker to help find network security gaps that create security exposure and risk.
Mainframe Pentesting
NetSPI provides valuable insight into your LPAR security, with actionable guidance on how to improve your mainframe security, and help to meet compliance requirements.
Virtual Desktop Pentesting
During virtual desktop penetration testing, NetSPI identifies vulnerabilities that provide unauthorized access to the operating system through desktops published via virtualization platforms. Additionally, NetSPI reviews the system configuration to identify vulnerabilities that could be used to break out of Citrix or VMware, escalate privileges, pivot into your network environment, or exfiltrate sensitive data.

Host-Based Pentesting
During host-based penetration tests, NetSPI security experts perform a deep dive review of baseline workstation and server images used to deploy systems to the corporate environment. This includes testing system drive encryption, group policy configurations, patch levels, service configurations, user roles, and more.
” ”
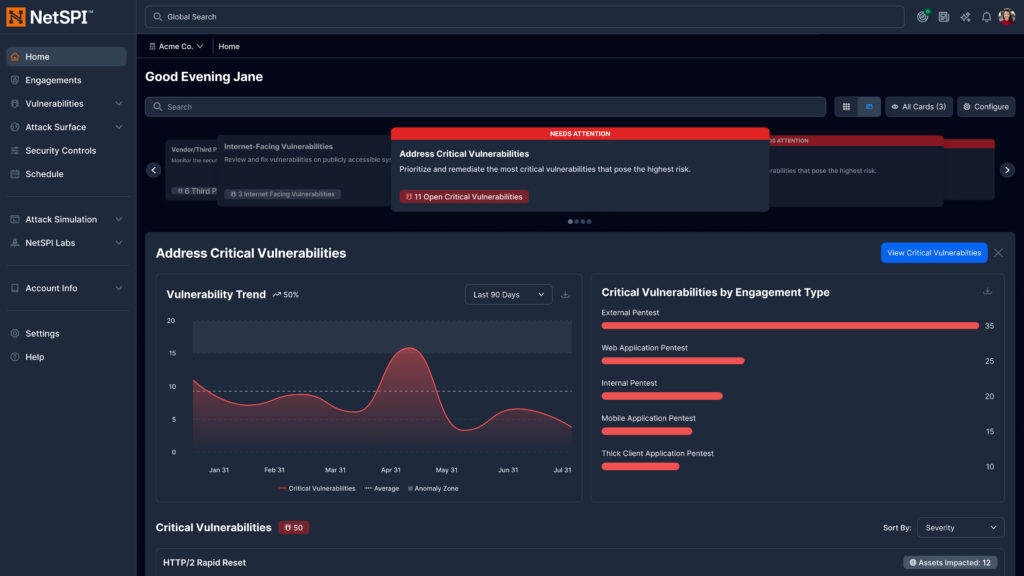
The New NetSPI Platform Experience
- Get answers to critical security questions faster, aligned to role and priorities
- Manage integrations, scans, and agents in one centralized workflow
- Accelerate detection, prioritization, and remediation across the attack surface
- Clearly demonstrate security outcomes to technical and executive stakeholders
“”
Network Pentesting Resources
15 Ways to Bypass the PowerShell Execution Policy
NetSPI security expert Scott Sutherland covers 15 ways to bypass the PowerShell execution policy without having local administrator rights on the system.
Set Sail: Remote Code Execution in SailPoint IQService via Default Encryption Key
NetSPI discovered a remote code execution vulnerability in SailPoint IQService using default encryption keys. Exploit details, discovery methods, and remediation guidance included.

CVE-2025-26685 – Spoofing to Elevate Privileges with Microsoft Defender for Identity
Discover how NetSPI uncovered and reported a vulnerability in Microsoft Defender for Identity that allowed unauthenticated attackers to perform spoofing and elevate privileges.
You Deserve The NetSPI Advantage
 Human-Led
Human-Led
- 350+ pentesters
- Employed, not outsourced
- Wide domain expertise
 AI-Accelerated
AI-Accelerated
- Consistent quality
- Deep visibility
- Transparent results
 Modern Pentesting
Modern Pentesting
- Use case driven
- Friction-free
- Built for today’s threats