External Network Penetration Testing
Comprehensive External Network Pentesting
Organizations face opportunistic and targeted attacks against their external facing assets, network systems, web applications, and cloud environments. It’s an always expanding attack surface. NetSPI’s approach to external network penetration testing enumerates your exposures, identifies critical vulnerabilities, and exploits them using the tactics, techniques, and procedures used by real-world threat actors.
What do NetSPI External Network Assessments test for?
Scanning internet-facing resources is a high priority, but a complete assessment of the hardness of your external network requires more. NetSPI’s expert network security testing probes external networks to identify vulnerabilities in protected systems across your cloud, network, application, and embedded systems.
-
Cross-site scripting (XSS)
-
Broken authentication & access control
-
Sensitive data exposure
-
Insecure deserialization
-
XML external entities (XXE)
-
Insufficient logging and monitoring
-
Components with known vulnerabilities
-
Security misconfiguration
-
Injection
“”
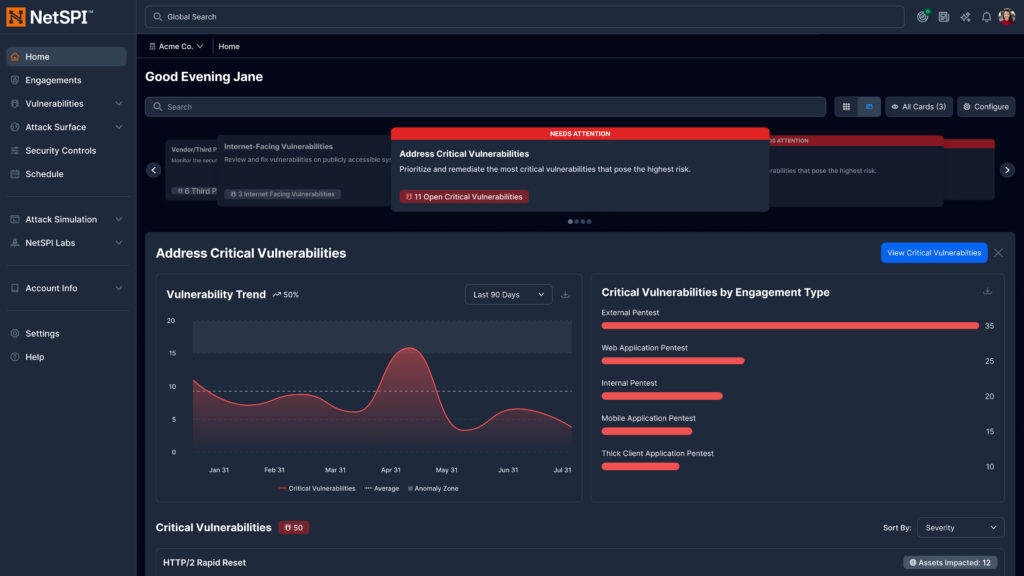
Continuous Pentesting Services Powered by NetSPI’s AI-Accelerated Platform
Each deployment brings the potential for new risks, making it harder for teams to maintain a clear view of security without continuous, automated insights. Automation only isn’t enough. AI-only solutions like Mythos overwhelm security teams with thousands of raw vulnerabilities and lack the context and prioritization needed to take action, creating more chaos than clarity.
“”
NetSPI doesn’t bolt AI onto existing scanners. Its systems are built around how LLMs actually reason, providing unprecedented depth and fidelity. It chains attacks, adapts mid-test, confirms findings and is grounded in decades of real-world pentesting data.
The New NetSPI Platform Experience
- Get answers to critical security questions faster, aligned to role and priorities
- Manage integrations, scans, and agents in one centralized workflow
- Accelerate detection, prioritization, and remediation across the attack surface
- Clearly demonstrate security outcomes to technical and executive stakeholders
“”
You Deserve The NetSPI Advantage
 Human-Led
Human-Led
- 350+ pentesters
- Employed, not outsourced
- Wide domain expertise
 AI-Accelerated
AI-Accelerated
- Consistent quality
- Deep visibility
- Transparent results
 Modern Pentesting
Modern Pentesting
- Use case driven
- Friction-free
- Built for today’s threats