NetSPI’s 6-Step Threat Modeling Process
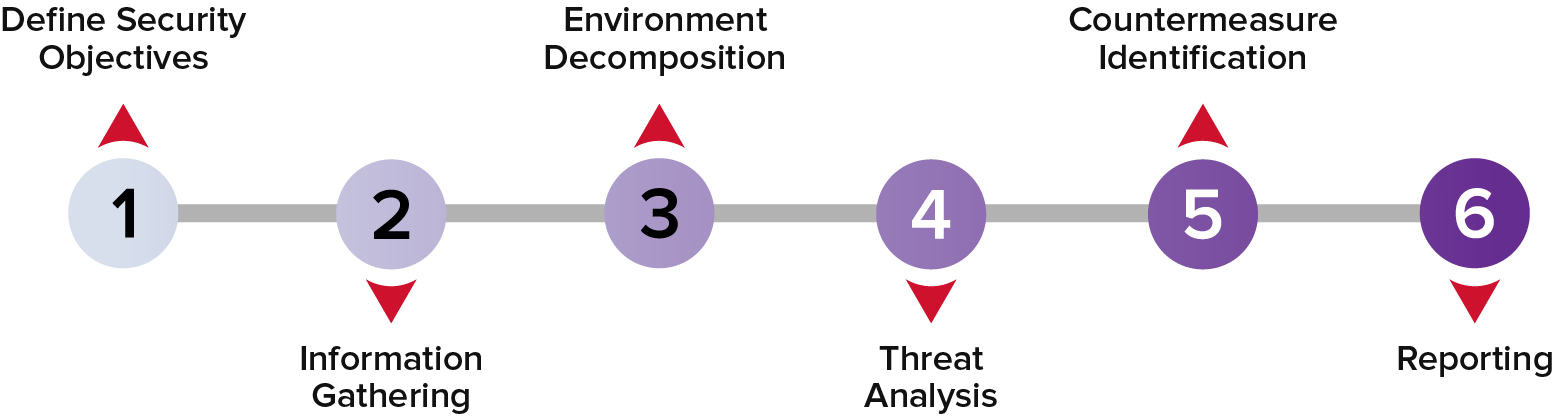
1. Define Security Objectives:
Establish specific security objectives for the engagement and prioritize in alignment with your company’s overall mission and risk tolerance.
2. Information Gathering:
NetSPI collects and reviews all available documentation. We also identify and interview system stakeholders such as: security personnel, developers, architects, business owners, project managers, operations staff, and more. These interviews are designed to provide information about both the architecture and context in which the system(s) function.
3. Environment Decomposition:
We build a component diagram of the most relevant deployment models and information flows between system components, then work to enumerate the system components and trust zones within the environment.
4. Threat Analysis:
Then, we develop a threat analysis based on the assets and system environment. Leveraging NetSPI’s extensive threat library, along with the client-provided information, we enumerate threats, classify severity, define attack scenarios, and identify additional security measurements that can be implemented based on business risks and organizational goals.
5. Countermeasure Identification:
We produce a threat traceability matrix by enumerating actions, devices, procedures, and techniques that prevent or mitigate threats to assets and system components.
6. Reporting:
Lastly, we produce a threat traceability matrix, mapping threats and threat scenarios to their trust zones, components, assets, and controls, and providing a summary of insufficient security controls and related threats.
Get The Threat Modeling Data Sheet
Identify potential threats and gain actionable information to enable strategic security decision-making.
Results Delivered in NetSPI’s PTaaS Platform
-
Real-Time ReportingGet notified of vulnerabilities in platform as they are found.
-
Remediation GuidanceVulnerabilities are delivered with remediation instructions and consultant support.
-
Project Management and CommunicationEffortlessly assign responsibilities, track remediation status, communicate with teams, and more.
-
Track and Trend DataAnalyze findings and discover trends over time.



