Dark Web Monitoring And Why Your EASM Strategy Depends On It

Most security professionals dedicate their efforts to protecting what they can see and control within their organization’s perimeter. They focus on securing customer data and intellectual property, conducting phishing awareness training, implementing multi-factor authentication, and ensuring proper password rotation policies. These defensive measures are undeniably important for protecting the assets you own and directly manage.
But what about the digital assets and data related to your organization that exist beyond your control?
This blind spot represents one of the most significant challenges facing modern enterprises. Attackers can detect and abuse exposed credentials within 5 minutes according to research done by Unit42.
This blind spot represents one of the most significant challenges facing modern enterprises. Attackers can detect and abuse exposed credentials within 5 minutes according to research done by Unit42. However organizations routinely discover they’ve been breached weeks or months after the fact, often learning about incidents only when their data surfaces on underground forums or third-party platforms like GitHub.
The reality is that your organization’s digital footprint extends far beyond your network boundaries, creating exposure through dark web marketplaces, data breaches, and public repositories that can leave your business vulnerable to sophisticated attacks. Today, NetSPI announced advancements to our External Attack Surface Management (EASM) offering, providing more visibility into external threats facing organizations. In the following sections, we will dig into these topics further.
The Expanding Attack Surface Challenge
Today’s business environments are increasingly distributed and interconnected. Cloud services, third-party integrations, remote work arrangements, and digital partnerships have created a complex web of relationships that traditional security perimeters cannot adequately protect. As organizations grow and evolve, their digital presence becomes more scattered across platforms they don’t control, creating blind spots that threat actors actively exploit.
The question isn’t whether your organization’s data exists outside your direct control; it’s whether you know where it is and what risks it poses. This is where continuous monitoring of external threats becomes not just valuable, but essential for proactive cybersecurity.
The question isn’t whether your organization’s data exists outside your direct control; it’s whether you know where it is and what risks it poses.
Dark Web Data: Understanding the Dark Web
The dark web serves as a thriving marketplace where cybercriminals buy, sell, and trade stolen data. This hidden network hosts forums and marketplaces where threat actors conduct business, featuring corporate credentials, customer databases, financial information, proprietary source code, and more. This information is often packaged and sold to other criminals who use it for targeted attacks, fraud, or further data theft.
Dark web exposures affect virtually every organizational stakeholder. Employees face identity theft risks, customers may experience financial fraud, and organizations face regulatory compliance issues and reputational damage. Executive leadership is particularly concerned because these exposures often indicate successful breaches that trigger disclosure requirements, regulatory compliance scrutiny, and financial consequences.
Information on the dark web doesn’t disappear. Once your data enters these underground markets, it can be resold, combined with other datasets, and used by criminals for highly targeted spear-phishing campaigns, business email compromise attacks, and social engineering schemes that traditional security measures struggle to detect. Early detection can mean the difference between containing a limited breach and experiencing a catastrophic security incident.
Effective dark web monitoring requires specialized tools and continuous surveillance capabilities that can identify mentions of their company, employees, customers, or proprietary information across various dark web platforms. When monitoring identifies your data, immediate action is critical, including credential resets, enhanced account monitoring, customer notifications where appropriate, and forensic investigation to understand how the breach occurred and prevent future incidents.
Breach Data: When Third-Party Incidents Affect Your Organization
Breach data encompasses information exposed through third-party security incidents that impact your organization indirectly. This includes breaches of vendors, partners, cloud services, or any external entity that processes your data or maintains access to your systems. These incidents create cascading effects throughout organizations, impacting IT teams who must assess exposure, legal teams facing regulatory obligations, and business leaders managing vendor relationships.
Third-party breaches often expose shared credentials and integration points that attackers exploit for lateral movement into your environment. Even without directly compromising your systems, the exposed information provides valuable intelligence for targeted attacks. Also, regulatory frameworks increasingly hold organizations accountable for third-party data handling practices, making breach exposure monitoring essential for compliance.
Comprehensive breach data monitoring requires tracking security incidents across your vendor ecosystem and maintaining detailed inventories of third-party relationships and data flows, along with automated systems that can correlate breach information with your specific risk profile. Response protocols should include immediate credential rotation, regulatory actions, enhanced monitoring of integration points, and vendor communication to understand exposure scope.
Public Data Exposure: When Internal Information Goes Public
Public data exposures occur when sensitive organizational information inadvertently becomes accessible through misconfigured cloud storage, accidental code repository commits, unsecured databases, employee oversharing on social platforms, or a variety of other ways. Unlike malicious breaches, these often result from human error or system misconfigurations but can be equally severe as threat actors actively scan publicly accessible information.
These exposures affect different stakeholders depending on the disclosed information. This can include development teams when source code is published, HR when employee information appears publicly, or sales teams when customer lists are exposed through misconfigured platforms. The distributed nature of modern work means virtually any employee can inadvertently create public exposures.
Public exposures provide attackers with detailed organizational intelligence about your infrastructure, processes, and relationships without requiring sophisticated hacking techniques, enabling more effective social engineering and targeted attacks. Search engines and automated scanning tools make it easy for threat actors to discover and exploit these exposures at scale.
Prevention requires technical controls, employee training, and continuous monitoring with visibility into public-facing assets and automated scanning capabilities that can identify sensitive information before malicious actors discover it. Response procedures should prioritize rapid remediation and removal requests, followed by investigation to understand how information became public and implementation of preventive controls.
The Path Forward: Continuous Threat Exposure Management
The modern threat landscape demands a fundamental shift from traditional perimeter-based defenses to continuous monitoring of external sources and proactive response capabilities that address emerging risks before they escalate.
This critical need is precisely why NetSPI has expanded our External Attack Surface Management solution to include comprehensive dark web, breach data, and public data exposure monitoring capabilities. By integrating dark web surveillance with our existing platform, organizations can now maintain complete visibility across their entire digital footprint, including the assets they control and the threats that exist beyond their boundaries.
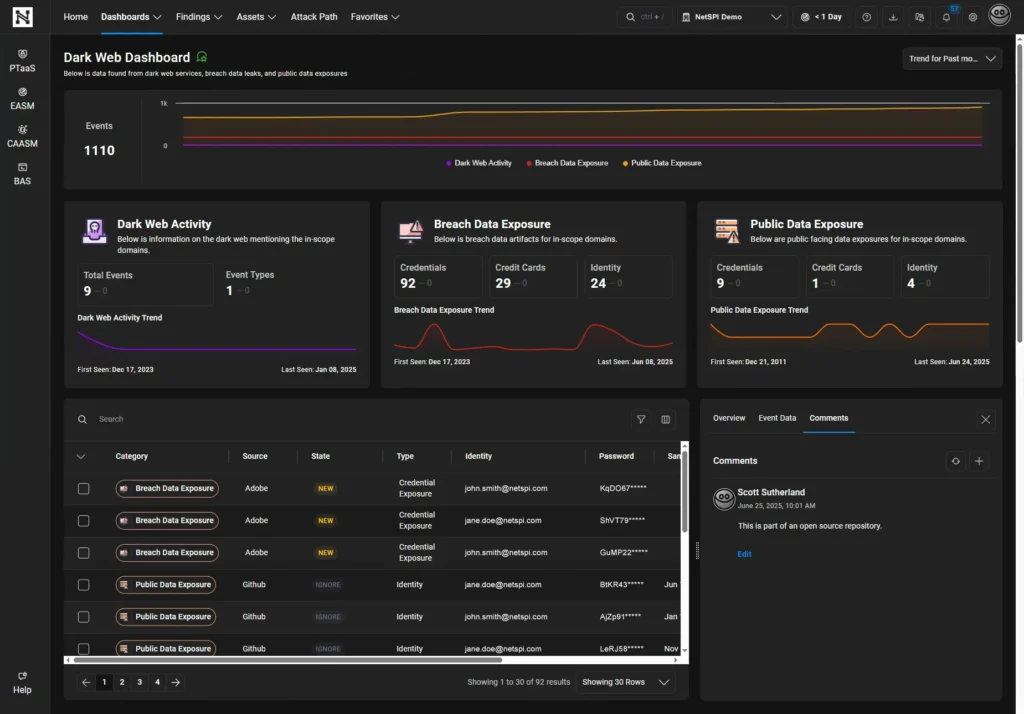
NetSPI EASM’s dark web monitoring represents the first of several new features designed to help security teams look beyond their environment’s borders, with data such as malware stealer logs, raw event data, identity exposures, leak sources, and more. This provides the real-time intelligence security professionals need to respond to threats within that critical window when attackers typically act on exposed credentials.
The question facing security leaders isn’t whether external threats will impact their organization; it’s whether they’ll detect and respond before attackers can exploit them. The time to expand your security vision beyond your borders is now. To learn more, request a demo of NetSPI EASM.
To learn more, request a demo of NetSPI EASM.
Explore More Blog Posts

Why Your Security Program Needs Domain Monitoring
NetSPI Domain Monitoring continuously discovers and assesses look-alike domains related to your organization, providing deep contextual intelligence including risk profiles, WHOIS records, IP details, DNS records, and certificate data. The NetSPI Platform streamlines response by allowing users to generate pre-filled takedown reports with all relevant evidence and technical details in a single click, enabling rapid action against high-risk domains.

Oracle WebLogic Server Proxy Plugin (CVE-2026-21962): Overview & Takeaways
CVE-2026-21962 allows an unauthenticated remote attacker to bypass security controls and potentially gain unauthorized access to backend WebLogic systems. Because these proxy plugins often sit in DMZ environments, the exposure is significant.

Rust’s Role in Embedded Security
Rust enhances memory safety in embedded systems, but rigorous security testing remains essential to address logic, hardware, and cryptographic vulnerabilities. Explore the benefits and key considerations of using Rust



