EPISODE 052 – High Stakes Security: Wynn Resorts CISO Covers Identity and Access Management and the Misrepresentation of Modern Hackers
Episode Details:
Show notes:
- 04:17 – Day in the life of a hospitality CISO
- 08:43 – Managing access with a custom-built identity orchestration platform
- 16:35 – Machine learning and artificial intelligence in IAM
- 22:00 – Getting started with the SANS 20 Critical Controls
- 23:13 – Casino hacking: It’s not as glamorous as you think
- 25:43 – Misrepresentation of the “modern hacker”
What does a day in the life of the Wynn Resorts CISO look like?
David loves the variety and challenge of his job because no day is ever the same. The ultimate compliment for him and the information security team is when customers have a great time without even noticing their efforts. It means they’ve delivered a seamless experience.
“The last thing they want to think about while they’re on vacation is their information security – if somebody’s going to steal their data from our company or from them while they’re on our site. We don’t want them to worry about that. We’re here to make sure that they’re protected.”
How have you seen Identity and Access Management (IAM) practices work and fail?
One of David’s passions in his career is the identity orchestration program he and his team built. It includes a control mechanism to ensure that people have the right access at the right time, as well as an automation process to take away permissions when they’re no longer needed.
“It’s making sure that we’re looking at identity literally every 24 hours and we’re running audit as fast as a computer can process it, so that if somebody creates an invalid account, we’re not 260 days out. We’re not 90 days out. We’re catching it that day or the next day.”
How do you envision the usage of machine learning and artificial intelligence in IAM?
It’s a coupling of IAM, user behavior analytics, and system behavior analytics that will be used more in the HR process, says David. It’ll be used to detect abnormal user behavior and trigger alerts for human intervention and to help create a process for provisioning and deprovisioning sensitive functions based on a person’s role.
“The more organizations take on this kind of work and build better integrations and capabilities to go into these single signs on and automation platforms, [the more] they’re going to build value into their own solutions that will give them a competitive advantage.”
Which cybersecurity frameworks have you found helpful for planning the evolution of a cybersecurity program?
There are several regulations such as PCI, NIST, and ISO that organizations must follow for security purposes, but David suggests following the SANS 20 Critical Controls to improve your security environment and prevent hacking.
“If every organization did those 20 critical controls, the security environment around the world would be so much better than it is today. The hackers would find a whole lot more trouble getting into organizations.”
With your experience in the hospitality industry, could you share interesting casino security control stories that you’ve seen or experienced?
The big signs outside casinos are often targeted by hackers, especially during events like DEFCON and Black Hat. It’s interesting that some hackers put their name on the signs, violating the anonymity in hacking, but David says that casinos are very diligent about security in Las Vegas.
“Some people view it as a job interview as opposed to a felony. They shouldn’t, because it’s really not a job interview.”
Misrepresentation of the “modern hacker” and how cybersecurity is portrayed in movies
The problem with Hollywood movies is that they depict the hacker lifestyle as cool and desirable, not that it’s illegal and can lead to incarceration.
“What they’re not portraying is that’s illegal. That’s unlawful. That’s going to lead to incarceration. I would much like to see Hollywood and those people flip around and idolize the guys who are being defensive for the company… make that the focus and the bad guys still look like bad guys.”
Connect with David Tyburski on LinkedIn to learn more about his work. Also, tune in for more episodes of Agent of Influence.
Explore More Podcasts
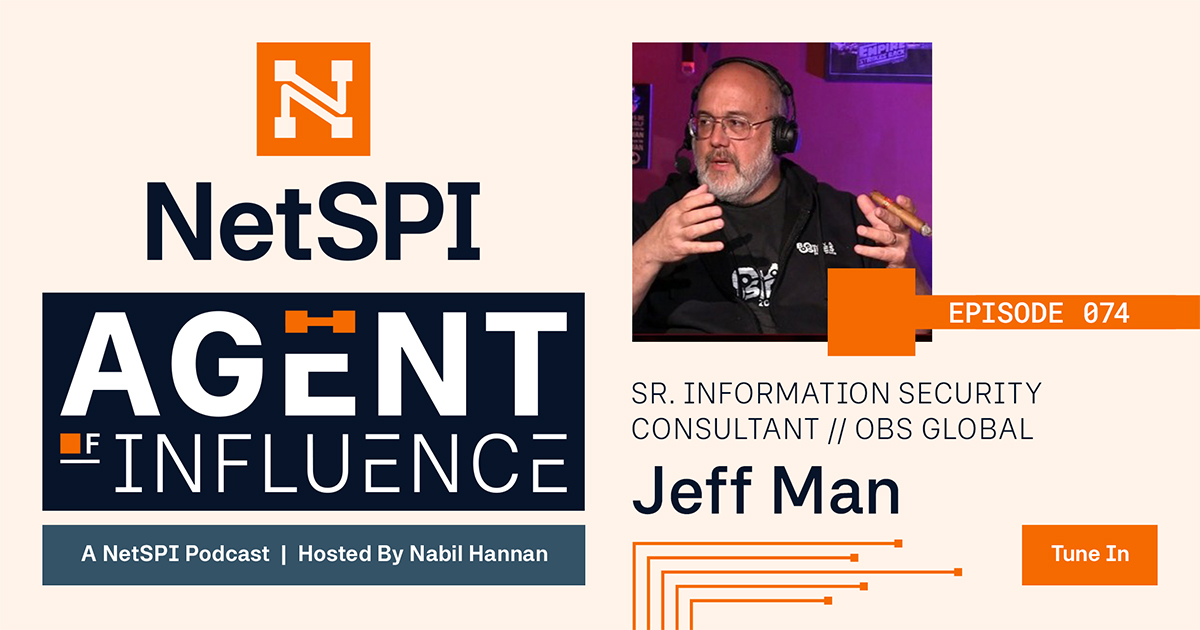
EPISODE 074 – Step into a Cybersecurity Time Machine
On Agent of Influence, Nabil Hannan and Jeff Man discuss industry fundamentals, the cryptologic cipher wheel, and empowering the next generation of cybersecurity professionals.

EPISODE 073 – Chief Persuasion Officer: The New CISO Mindset
Explore the evolving CISO role, AI in cybersecurity, career advice, and proactive security with Rick McElroy on the Agent of Influence podcast.

EPISODE 072 – Cybersecurity Lessons on the Path to Private Equity
Explore how private equity and cybersecurity intersect with Paul Harrigan of KKR. Learn strategies for managing risks, M&A diligence, and aligning security with growth.


