Internal Network Penetration Testing
Comprehensive Internal Network Security Testing
Improve network security and reduce organizational risk with NetSPI’s security experts. Internal threats and cloud-based vulnerabilities create security risks when they extend into hosted environments with ties to internal networks. NetSPI’s internal network penetration testing simulates the actions of a skilled attacker and helps you find network security gaps that create security exposure and risk.
OWASP Top 10 Coverage
What do NetSPI Internal Network Assessments test for?
Our approach to internal network penetration testing is based on best practices, including NIST SP 800-53, PCI DSS, OWASP Top 10, and the MITRE ATT&CK framework to encompass:
-
System & Service Discovery
-
Automated Vulnerability Discovery
-
Network Protocol Vulnerability Discovery
-
Web application Vulnerability Discovery
-
Active Directory Vulnerability Discovery
-
Segmentation testing for PCI DSS compliance
-
Online password auditing of available interfaces
-
Offline password auditing of AD Accounts
-
Sensitive networks, systems, and data access
-
System & Domain-level privilege escalation
-
Vulnerability exploitation & verification
-
False positive removal
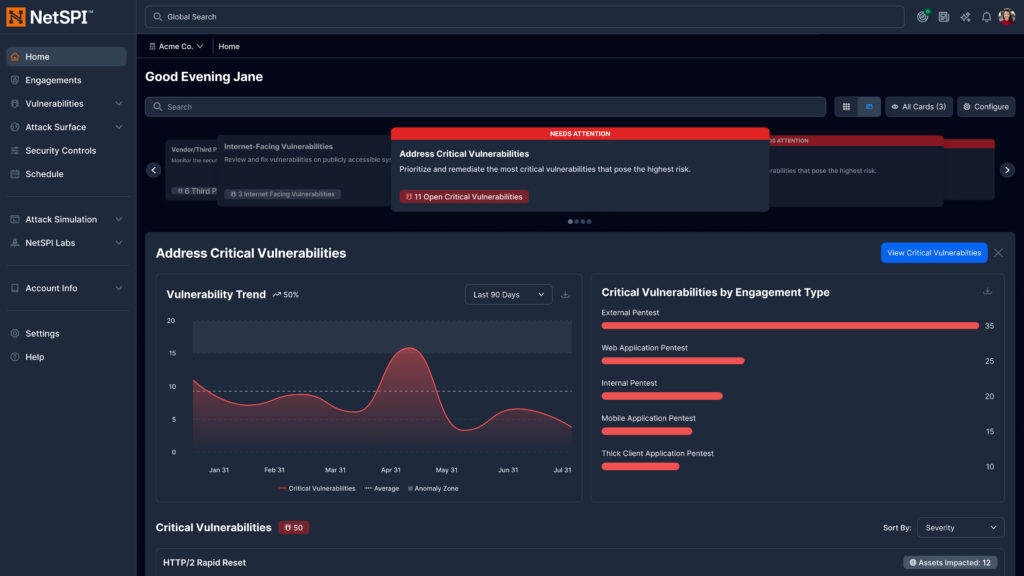
The New NetSPI Platform Experience
- Get answers to critical security questions faster, aligned to role and priorities
- Manage integrations, scans, and agents in one centralized workflow
- Accelerate detection, prioritization, and remediation across the attack surface
- Clearly demonstrate security outcomes to technical and executive stakeholders
“”
You Deserve The NetSPI Advantage
 Human-Led
Human-Led
- 350+ pentesters
- Employed, not outsourced
- Wide domain expertise
 AI-Accelerated
AI-Accelerated
- Consistent quality
- Deep visibility
- Transparent results
 Modern Pentesting
Modern Pentesting
- Use case driven
- Friction-free
- Built for today’s threats