Cyber Insights From Our Security Experts
At NetSPI, we’re on the front lines of safeguarding systems — just like you. Catch up on our team’s stories, advice, and proactive security insights below.

Internal Network Pentesting
Secure your internal networks against evolving threats with actionable insights discovered through expert-led penetration testing.

Gartner Report for Penetration Testing as a Service (PTaaS)
Download the full Gartner® report for comprehensive insights on PTaaS trends, benefits, and implementation considerations.

NetSPI Continuous Pentesting
NetSPI launches AI-powered Continuous Pentesting to help organizations validate and reduce risk through their Human-led, AI-accelerated platform that supports agentic MCP integrations.

External Network Pentesting
Secure your external networks against evolving threats with actionable insights discovered through expert-led penetration testing.

AI-Enabled Penetration Testing
NetSPI’s AI-powered platform and expert-led AI/ML security services enable faster innovation without introducing new risks.

App Intruders: How to Build an App Pentesting Program
This guide delivers actionable insights on developing a strong App Pentesting strategy, directly from NetSPI’s Application Service Line Directors.
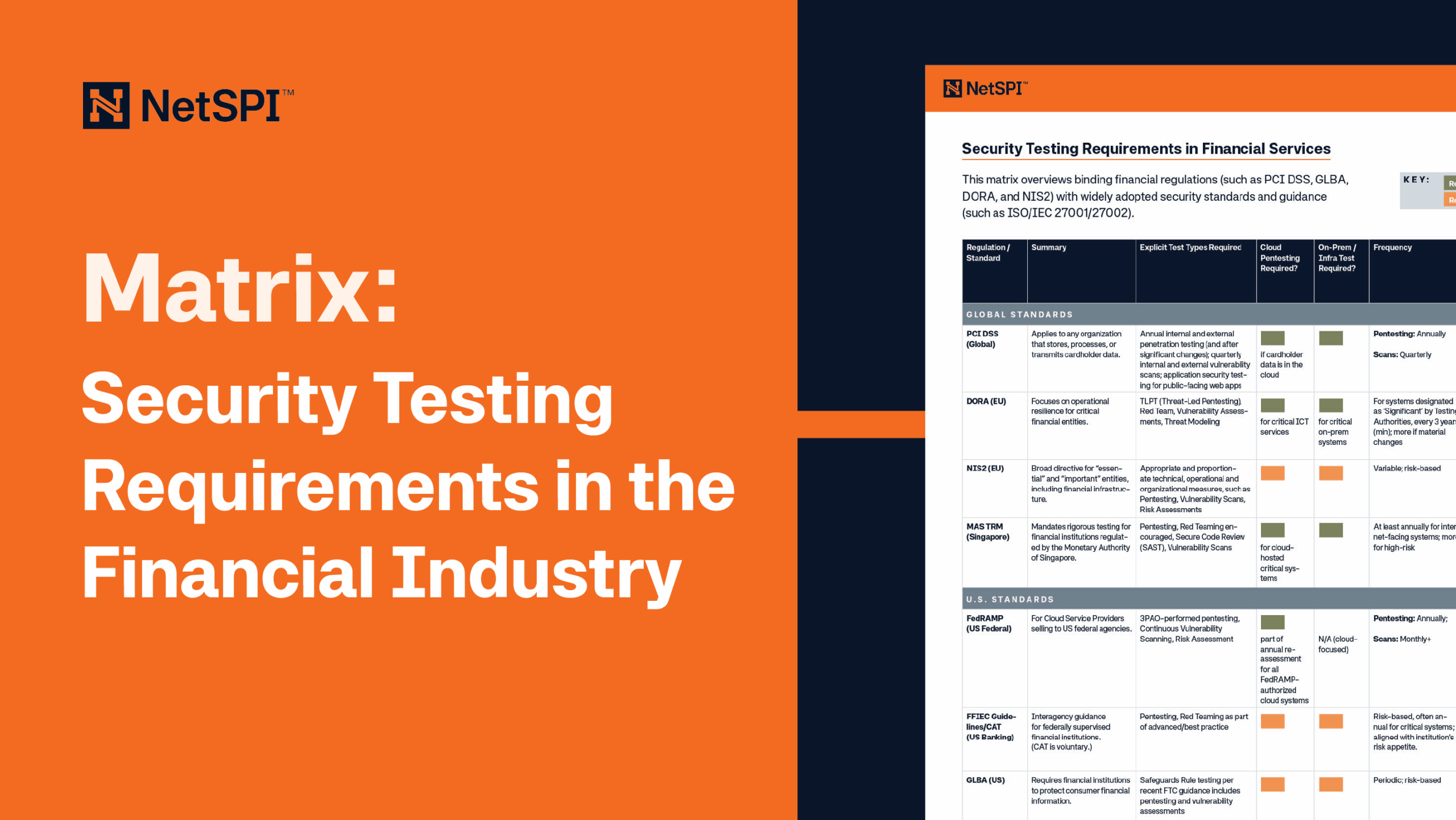
Financial Industry Security Testing Requirements Matrix
This comprehensive matrix breaks down financial industry security testing regulations (such as PCI DSS, GLBA, DORA, NIS2, and ISO/IEC 27001/27002)

2026 Cybersecurity Trends
Dive into the top cybersecurity trends that are shaping the industry in 2026 and beyond directly from NetSPI’s leading security experts.

API Security Best Practices
APIs are central to digital business operations, and their rapid adoption expands the attack surface, making these targeted API security testing best practices essential.

Ready for Red Teaming?
Watch this session with Red Teaming experts Giles Inkson (Director, Red Team & Adversary Simulation) and Karl Fosaaen (VP of Research) to get their practical playbook on building scenarios.
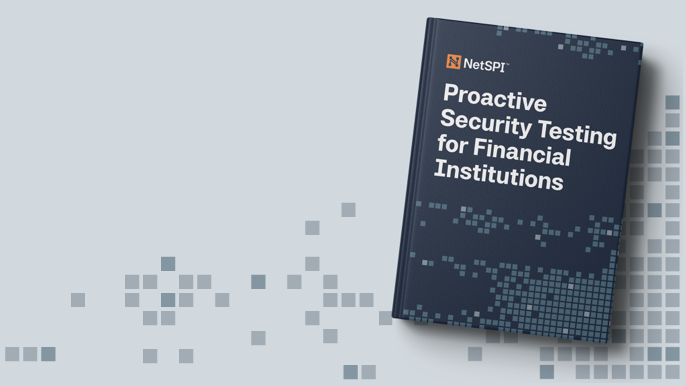
Proactive Security Testing for Financial Institutions
With 54% of financial institutions experiencing attacks in 2025, it’s imperative for this industry to adapt modern proactive testing strategies to stay a step ahead.

Virtual Application Penetration Testing
Secure your virtual applications against evolving threats with actionable insights discovered through expert-led penetration testing.