Unique Encryption Keys Not So Unique

You may have seen some of the recent articles regarding a research paper that documented a discovered flaw in some commonly used encryption schemes, including those used for online transactions. I think it’s important to point out that the sky isn’t falling. That said this may be a good time to check your encryption processes and determine if this really applies to you. Within the paper the researchers determined using 1024-bit RSA provides “99.8% security at best.” This isn’t systemic for all processes; the researchers did not find the same problem after looking at 5 million OpenPGP keys (which is the source of the paper’s title). Without getting too far into the technical aspects of the paper, the researchers found that numbers used in the creation of the keys weren’t so random after all. This culminated in critical parts of the algorithm being similar to another key. Thus the keys were the same. What does this mean for you and your organization? Time to check your encryption settings and certificates. If you outsource this as part of your e-commerce solution, have the vendor validate their settings. If you use RSA keys you might consider changing them, of course this isn’t something that most organizations can/will do with minimal impact. One of the big questions I foresee is if this will affect your PCI Compliance? At this time no. While many recognize that risk posed by the redundant keys found by the researchers is significantly less than it might otherwise be, you most likely will be safe. However this is something to keep tabs on. If further research continues to find issues with how the prime numbers are generated within the methods, it may be time to start the switch. Overall, it’s important to remember that if you use the RSA keys, the sky isn’t falling all around you, just 0.2% of it is.
Explore More Blog Posts
AI Fools Week: Don’t Let AI Fool Your Pentesting Strategy
AI is transforming penetration testing. It promises speed, scale, and automation. But here is the catch. When used in isolation, AI can create a false sense of security. And that is no joke. A modern approach to pentesting requires balance, combining the efficiency of AI with the expertise of human testers. Without that balance, organizations risk missing what matters most.

LiteLLM Supply Chain Compromise
A supply chain attack compromised LiteLLM versions 1.82.7 and 1.82.8 on PyPI, exfiltrating credentials and secrets to an attacker-controlled server.
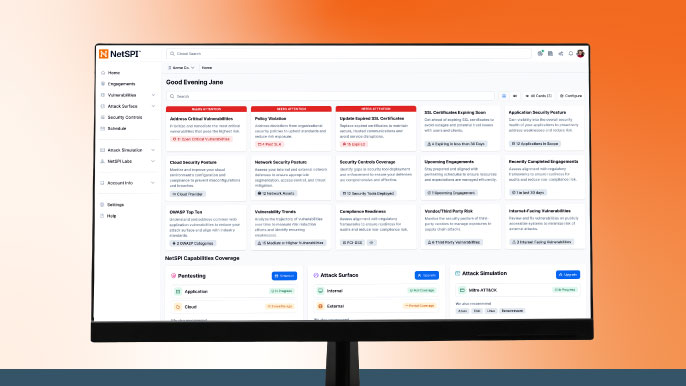
Meet NetSPI’s Modern Pentesting Experience: Use Case-Driven, AI-Accelerated
The new NetSPI experience represents the next evolution of pentesting—smarter, faster, and designed for scale.