
NetblockTool: The Easy Way to Find IP Addresses Owned by a Company
TL;DR
Use NetblockTool to easily dump a unique list of IP addresses belonging to a company and its subsidiaries.
Download the tool here: https://github.com/NetSPI/NetblockTool
The Problem
A problem that I was frequently running into for both offensive and defensive roles is determining the IP addresses that a company owns and uses. Traditionally, gathering a list of IP addresses a company owns is a long and very manual process. Various sources need to be used like Google, ARIN, WHOIS, IPinfo, Censys, and Shodan. The list goes on.
Thankfully, there are some automated tools that exist that make this process a bit easier. Recon-ng is one of these tools but it isn’t perfect, and while it does a lot of things well, easily gathering a complete list of netblocks for a company is not one of those things. This is where NetblockTool comes in.
The Solution: NetblockTool
Written as a standalone Python script, NetblockTool is designed to fill in this tooling gap.
For blue team users, simply provide the name of your company and receive a list of unique netblocks, ranked by the likelihood that the returned netblock belongs to your company.
For red team users, use NetblockTool to gather IP ranges, points of contact, and even netblocks belonging to your target’s subsidiaries.
Getting Started
Getting started is easy. Simply clone the repository, install the requirements, and you’re ready to start using NetblockTool.
git clone https://github.com/NetSPI/NetblockTool.git cd NetblockTool && pip3 install -r requirements.txt python3 NetblockTool.py -v Company
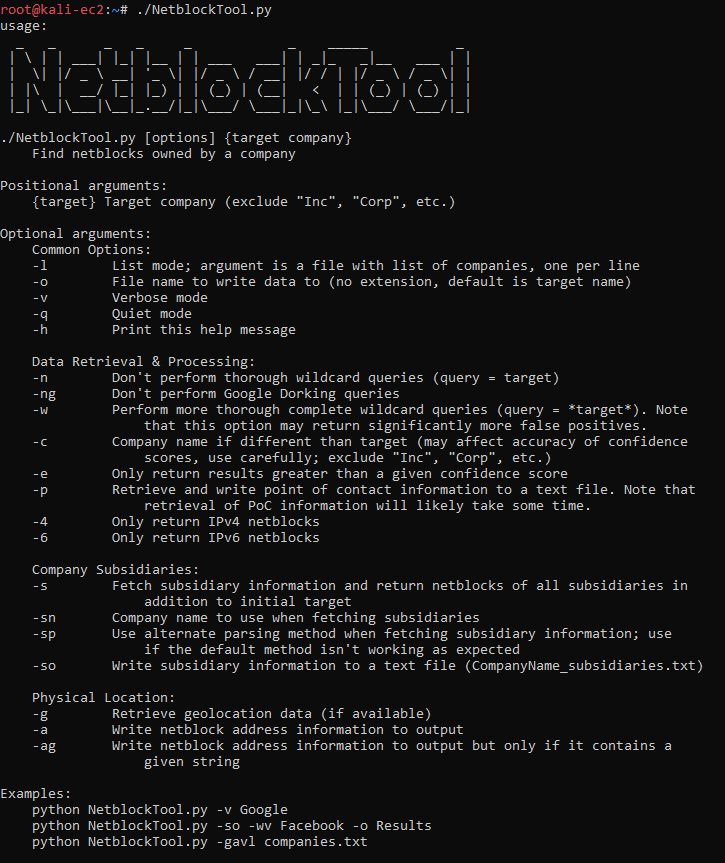
How does it work?
NetblockTool uses several data sources to gather netblocks that a company may own, which include Google dorking, the ARIN database, the ARIN API website, and IPinfo. Since public websites are being scraped, there is no API key needed for any site when using NetblockTool.
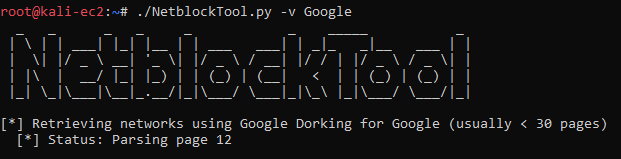
First, the user provides a target company. NetblockTool then scrapes Google using a Google dork to retrieve networks that IPinfo knows about.
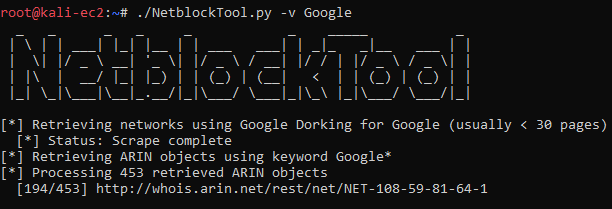
Next, the ARIN database is queried by sending the same traffic a normal user would send by visiting their website and manually searching for a company. The results are then scraped for ARIN objects (like networks and company contacts) and the objects are visited and further scraped. The advantage of this method is that more results are provided than just directly querying the database using their APIs.
After all sources have been scraped, each discovered netblock is deduplicated and assigned a confidence score that it belongs to the company. The score is largely based on the name of the netblock, the type of ARIN object it is (either ASN, network, or a leased range known as a customer), and the address linked to the netblock.
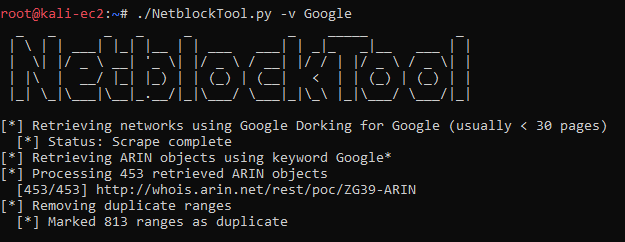
From here, further operations are then performed that are based on the user’s arguments, such a retrieving geolocation data for each IP.
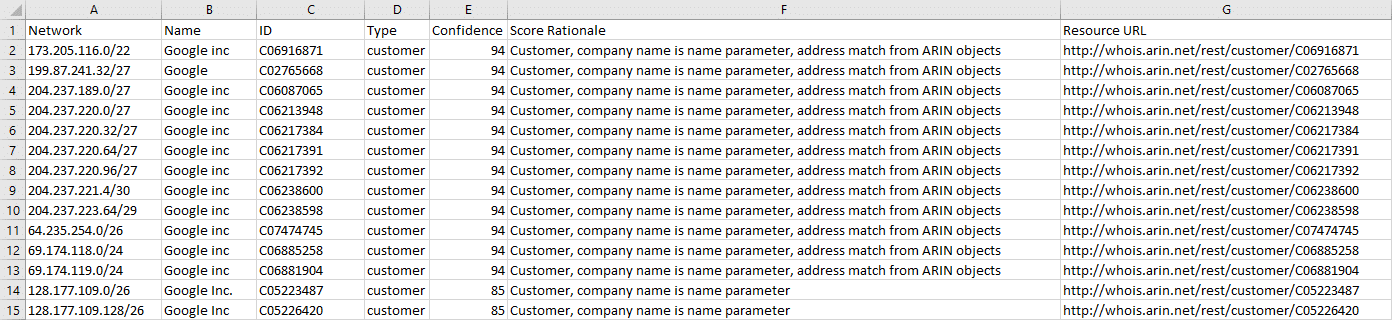
Finally, the total number of addresses is printed and the results are written to a CSV. The first 15 rows for Google are shown below.
Subsidiaries
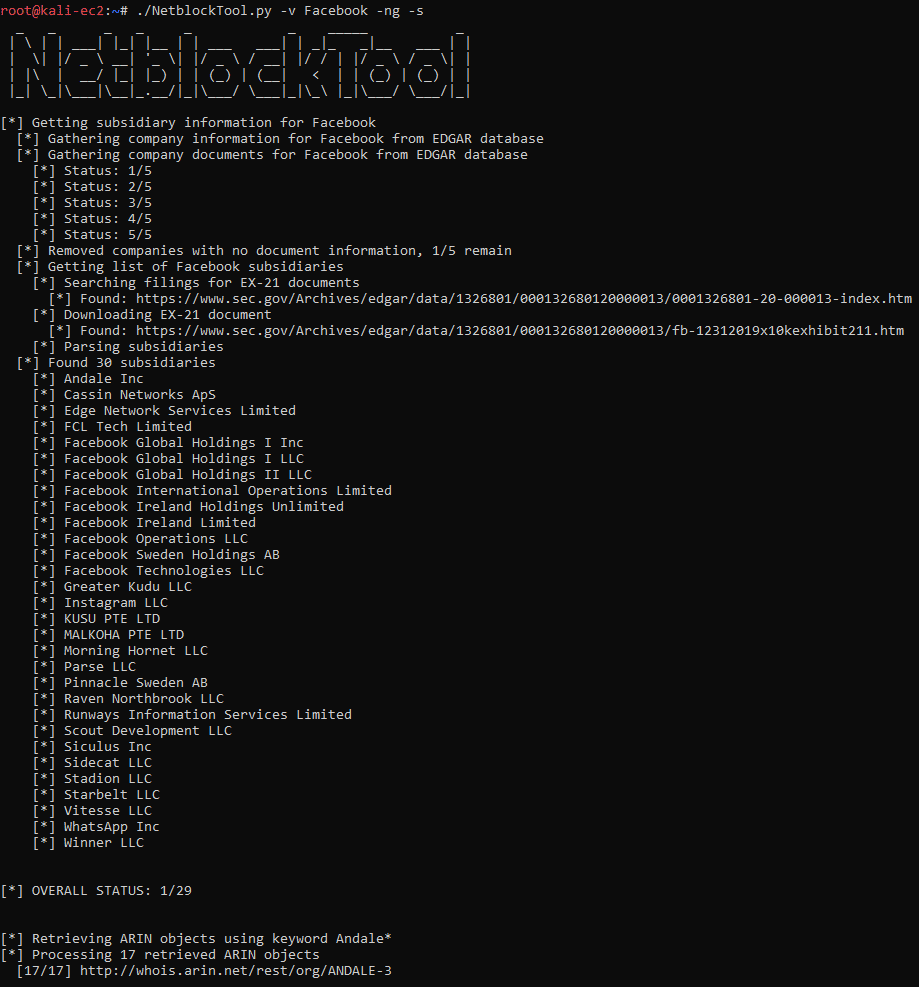
What if a company has subsidiaries and has netblocks registered to them? NetblockTool has you covered. It’s able to automatically query the Securities and Exchange Commission’s public database to retrieve a list of possible subsidiaries and then enumerate the subsidiaries’ netblocks.
Common Use Cases
There are many different ways of getting the data you desire from NetblockTool, but the easiest way of running the tool is simply:
python3 NetblockTool.py -v Company
If you want to extract netblocks owned by your target company’s subsidiaries, specify that flag:
python3 NetblockTool.py -v Company -s
Extracting point of contact information can also be helpful:
python3 NetblockTool.py -v Company -p
Or, if you want to get as much information as possible, including netblocks found using wildcard queries, points of contact, geolocation data, and physical addresses:
python3 NetblockTool.py -wpgav Company -so
Conclusion
Whether you need to find the netblocks your employer owns or find the netblocks for your next red team engagement, NetblockTool is your quick and easy solution. Give it a shot and see if you find it useful.
Explore More Blog Posts

Extracting Sensitive Information from Azure Load Testing
Learn how Azure Load Testing's JMeter JMX and Locust support enables code execution, metadata queries, reverse shells, and Key Vault secret extraction vulnerabilities.

3 Key Takeaways from Continuous Threat Exposure Management (CTEM) For Dummies, NetSPI Special Edition
Discover continuous threat exposure management (CTEM) to learn how to bring a proactive approach to cybersecurity and prioritize the most important risks to your business.

How Often Should Organizations Conduct Penetration Tests?
Learn how often organizations should conduct penetration tests. Discover industry best practices, key factors influencing testing frequency, and why regular pentesting is essential for business security.