Top Security Takeaways from Black Hat USA 2022 and DEF CON 30

With another year at Black Hat USA and DEF CON behind us, it’s time to reflect on some of the top takeaways, trending themes, and noteworthy best practices overheard across Vegas. In case you missed it, here’s what we were up to and what caught our attention at this year’s conferences:
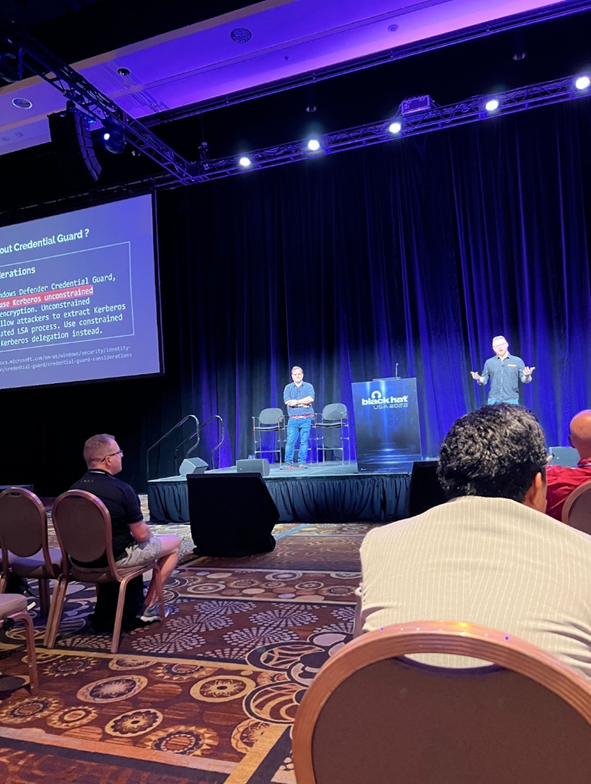
NetSPI’s Nick Landers Briefs Black Hat Attendees on the Latest Kerberos Research
NetSPI’s Head of Adversarial R&D Nick Landers presented his latest research on Kerberos alongside James Forshaw, security researcher at Google Project Zero.
Nick and James’ research revealed that while Kerberos should be the recommended long-term solution for network authentication in Windows networks, it shouldn’t be considered more secure than its predecessors. What they uncovered is that Kerberos is a complicated protocol, and there has been little deconstruction on how a local machine handles it. This allowed them to expose several bugs within it.
A key takeaway Nick shared is that security teams must look to develop a fundamental understanding of each protocol and how they come into play. Teams shouldn’t just look for vulnerabilities; looking for a deeper understanding of how a protocol works will allow teams to better understand its risk locations.
Big picture, Nick hopes to bring further awareness to Kerberos security challenges and “hopes the talk will spur security and network administrators to brush on their Kerberos knowledge to better harden their systems.” The session slides are now available, or read more in Dark Reading here: “Abusing Kerberos for Local Privilege Escalation.”
The Launch of New, Open-Source Tools & Greater Industry Collaboration
On the first day of Black Hat, we announced the release of two new open-source penetration testing tools developed by NetSPI Senior Director Scott Sutherland. The tools, PowerHuntShares and PowerHunt, help defense, identity and access management (IAM), and security operations center (SOC) teams discover vulnerable network shares and improve detections.
PowerHuntShares is focused on identifying shares configured with excessive permissions and providing data insight to understand how they related to each other, when they were introduced into the environment, who owns them, and how exploitable they are.
PowerHunt is a threat hunting framework that can be used to quickly collect artifacts commonly associated with malicious behavior. While it calls out suspicious artifacts and statistical anomalies, its greatest value is simply producing data that can be used by other tools during threat hunting exercises.
These new tools emphasize the importance of more open-source collaboration in the information security community. Working together to solve some of the industry’s most pressing problems was a powerful theme at this year’s Black Hat, not only with the release of Scott’s tools, but also with the announcement of The Open Cybersecurity Schema Framework, an open project to develop a single, open standard for sharing data. We applaud and support the Open Cybersecurity Schema Framework as a step in the right direction to advance community collaboration.
Penetration Testing Services Continue to Be a Top Priority
As cybersecurity budgets are scrutinized, penetration testing continues to be top of mind for Black Hat attendees. In fact, from our conversations at the NetSPI booth and throughout the show floor, many security teams are looking to complete penetration testing exercises before the end of the year and recognize it as a top priority in their security strategy.
From a managed security service provider (MSSP) perspective, they are handling an increasing amount of requests from their customers asking for penetration testing, as they realize the value such exercises can bring to an organization when strengthening its security posture.
While discussing penetration testing services, many attendees on the show floor agreed that there’s an increased focus on continuous testing, and the one unique differentiator in any security service, including pentesting, is the human element – talented people on the front lines working to ensure organizations are properly protected and filling the gaps that tools leave behind. We discuss this topic in one of our recent blog posts: Technology Cannot Solve Our Greatest Cybersecurity Challenges, People Can.
Cloud Security Takes Center Stage as Threats Skyrocket
At DEF CON’s Cloud Village, NetSPI Senior Director Karl Fosaaen provided a comprehensive review of the security pitfalls within Azure Automation accounts from his perspective as a cloud pentester. In this presentation, Karl also shared an overview of Azure’s permissions model, including security principles and roles, to help people unfamiliar with the topic gain a better foundational knowledge of it.
Overall, the presentation dissected how Automation Accounts may be targeted by attackers and pentesters alike, highlighting a range of vulnerabilities and attacks. Karl left the audience with a plethora of potential Automation Account vulnerabilities to find and secure in their own environments as cloud security threats continue to expand. The session slides are now available here.
In addition to Karl’s talk at DEF CON 30, Thomas Elling, Senior Director of the cloud pentesting practice at NetSPI, joined industry experts from Immuta, OneSpan, Code42, Netskope, and Obsidian in a virtual media panel hosted by Inkhouse in the week prior to Black Hat USA. During the talk, the group outlined the top cloud security threats affecting organizations worldwide, as well as what’s in store for cloud security in the years to come. You can read up on the panel’s main takeaways in this SDxCentral piece: Decentralization Haunts Security, Cloud Transitions.
More Diversity and Inclusion Necessary in the Cybersecurity Industry
At DEF CON’s Girls Hack Village, NetSPI Managing Security Consultant Melissa Miller explored a prevalent topic for women across many industries – imposter syndrome.
During the presentation, Melissa spoke about her personal experiences as a woman navigating a career in cybersecurity and discussed the characteristics of a healthy work environment. She also shared tips on how to spot imposter syndrome, along with immunization strategies and key techniques to identify your strengths and weaknesses and use that information to pursue and achieve your career goals.
Melissa also participated in a panel around diversity in the cybersecurity industry. In this talk, Melissa highlighted that there needs to be more openness around the concept of variety, understanding of people’s differences, and an earnestness to gain different perspectives to lead to more creative problem solving.
Melissa also stressed that diversifying the cybersecurity industry would reduce the ‘boys club’ stigma that many people associate with it, helping to encourage diverse people to pursue cybersecurity-related degrees, creating better growth and diversity in the cybersecurity workforce as a result.
Both of these presentations echoed a major sentiment at Black Hat USA and DEF CON 30 this year around creating more diversity and inclusivity in the cybersecurity industry, especially as recruiting talent remains a key challenge for the cybersecurity industry.
Live Social Engineering at DEF CON 30
NetSPI consultants enjoyed the social engineering village at DEF CON 30 and where NetSPI’s on-site social engineering lead Dalin McClellan volunteered. At the village, they cold-called businesses in-real time to see if they could get them to share sensitive information. In one instance, the employee disclosed information around building security, where the cameras were, how badging worked, where employees kept their belongings on shift, and more.
Social engineering, specifically phishing, remains the top attack vector for breaches today. NetSPI’s social engineering pentesting team is doing some really cool work in this space to help organizations prevent and prepare for social engineering attacks. Read about a recent on-site engagement in Dalin’s blog, Not Your Average Bug Bounty: How an Email, a Shirt, and a Sticker Compromised a High Security Datacenter.
Black Hat and DEF CON are Back in Full Swing
In addition to the news announced and rumblings overheard at Black Hat, our team also noticed that Black Hat and DEF CON were back in full swing, with a crowded show floor, bustling briefing halls, and the industry buzzing in Las Vegas once again.
Amid the crowds, vendors tried to stand out on the show floor with some attention-grabbing activities, like a boxing ring. Several booths had the words “attack surface” front-and-center, proving that Attack Surface Management has become an increased priority for security teams.
With these major security events now behind us, it’s important for the security industry to continue raising awareness and spreading education about some of the important topics discussed on the show floor. As cybercriminals become more sophisticated and well-funded and organizations prioritize cybersecurity, we’ll need continuous collaboration in the industry to better bolster security measures, as well as increase diversity to help amplify and expand defense teams.
What major topics caught your attention at Black Hat or DEF CON? Share them with us on Twitter or LinkedIn.
Explore More Blog Posts
CVE-2026-41940 cPanel & WHM Authentication Bypass Overview and Takeaways
cPanel has disclosed a critical authentication bypass vulnerability affecting cPanel & WHM and WP Squared, tracked as CVE-2026-41940 (CVSS 9.8). The flaw allows a remote, unauthenticated attacker to gain root-level administrative access by injecting arbitrary values into a server-side session file, effectively bypassing all credential checks.

Walking Through an Attack Path with ForceHound
In Part 2 of the series, Weylon covers how to use ForceHound to visualize Salesforce attack paths in BloodHound CE, identify transitive privilege escalation, and legacy Connected App exposures.

Auditing Salesforce Permission Hierarchies with ForceHound
Discover how ForceHound automates the collection of profiles, permission sets, and connected apps to reveal the true trust boundaries of your Salesforce organization.