
API -
NetSPI evaluates target APIs across the entire stack to help your security and development teams inventory and evaluate APIs for security vulnerabilities. This comprehensive approach combines manual expertise with automated tools to identify vulnerabilities that can compromise your applications and data. Five key API pentesting focus areas include:
-
1. Authorization Flaws
-
2. Injection Vulnerabilities
-
3. Data Exposure & Privacy
-
4. Business Logic & Rate Limiting
-
5. Security Misconfigurations
Mobile App Pentesting
NetSPI tests your Android & iOS mobile apps for vulnerabilities, including the OWASP Mobile Top 10, and mobile security controls across 4 essential areas:
-
Mobile App File System
-
Application Memory
-
Network Communications
-
Graphical User Interface
Resource Downloads
""
According to Gartner, “Organizations face the challenge of having many applications to test, but limited budget and resources to support manual penetration tests, resulting in visibility gaps. Major changes, newly released vulnerabilities and other exposures often remain untested until the next annual cycle."
- Gartner, Inc. Strengthen Critical Applications With an Effective Penetration Testing Program
Dhivya Poole, Aaron Lord, Niyati Daftary, 11 April 2025
Gartner is a trademark of Gartner, Inc. and/or its affiliates
Virtual Application Pentesting
NetSPI identifies the risks specific to applications published through virtualization platforms, as well as evaluates target virtual applications across the entire framework and application stack. Our approach identifies critical vulnerabilities including broken object-level authorization, function-level access control issues, unrestricted resource consumption, and security misconfigurations that could compromise your virtual apps.
""
Human-Driven Automated Pentesting
NetSPI’s Human-Driven Automated Pentesting (H-DAP) is designed to provide a lighter touch manual assessment across a broader range of web applications. H-DAP uses industry standard DAST scanning tools paired with targeted manual penetration testing, allowing companies to rapidly test a portfolio of applications and improve coverage.
""
Application Pentesting
Testing and Reporting
Other Vendors
Program and findings management


Program and findings management


Remediation testing


Remediation testing


Trend analysis and real-time dashboards


Trend analysis and real-time dashboards


PDF reports


PDF reports


Other Vendors
Asset inventory and deduplication


Asset inventory and deduplication


Vulnerability Prioritization
Other Vendors
Based on exposure, impact, exploitability
(CVE, CVSS, CPE, EPSS, KEV, and more)

Based on exposure, impact, exploitability
(CVE, CVSS, CPE, EPSS, KEV, and more)

Other Vendors
Self-service playbooks & lightweight agent execution

Self-service playbooks & lightweight agent execution

Automated detection verification

Automated detection verification

Vendor coverage comparison

Vendor coverage comparison

Other Vendors
Open API


Open API


Assets, IAM, Detective Controls & More

Assets, IAM, Detective Controls & More

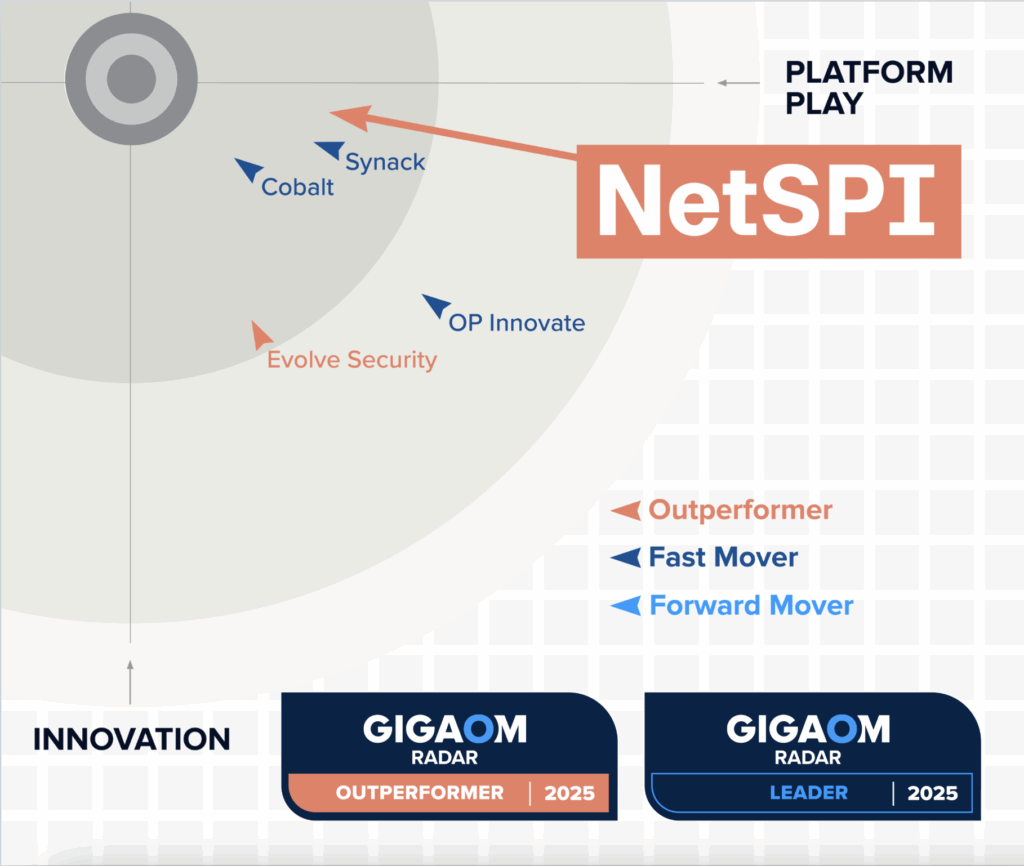
You Deserve The NetSPI Advantage
 Human-Led
Human-Led
- 350+ pentesters
- Employed, not outsourced
- Wide domain expertise
 AI-Accelerated
AI-Accelerated
- Consistent quality
- Deep visibility
- Transparent results
 Modern Pentesting
Modern Pentesting
- Use case driven
- Friction-free
- Built for today’s threats
 Thick Client
Thick Client 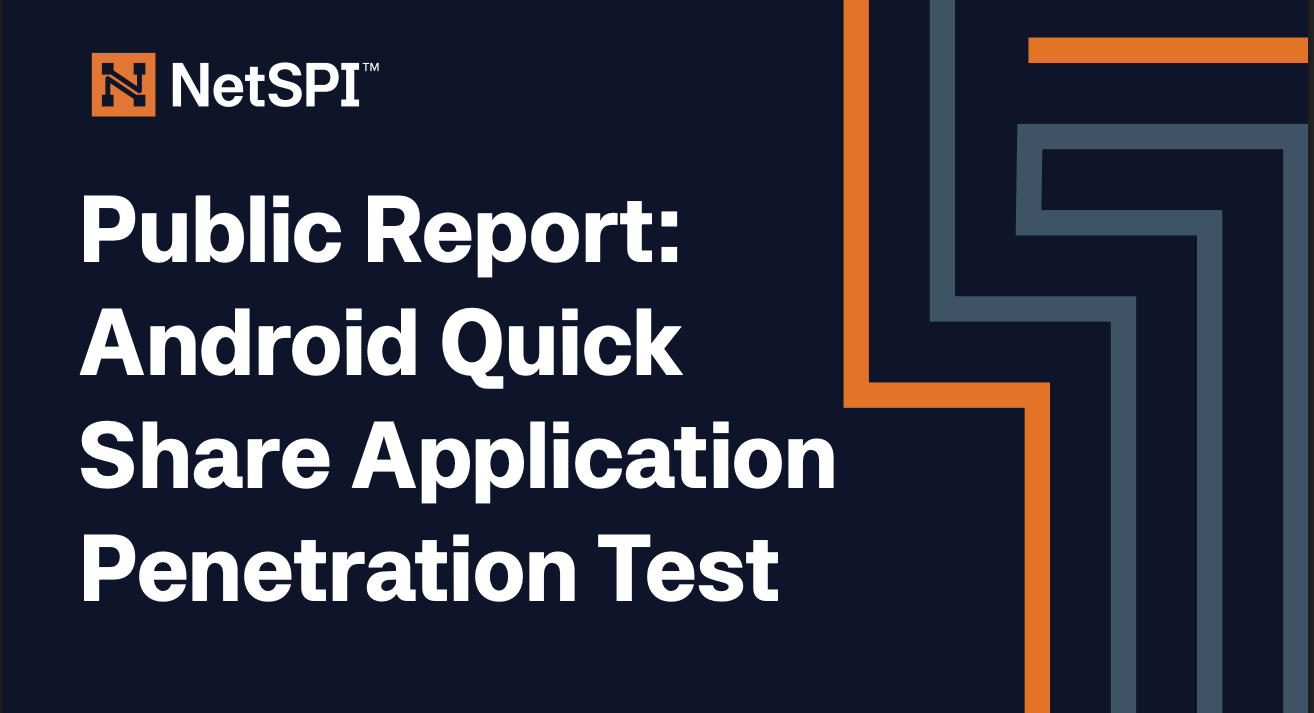
 API - Data Sheet
API - Data Sheet  H-DAP Solution Brief
H-DAP Solution Brief 



 Static Analysis
Static Analysis 