NetSPI Penetration Testing as a Service (PTaaS)
The NetSPI approach to Penetration Testing as a Service makes our expert penetration testing team available for you when you need it.
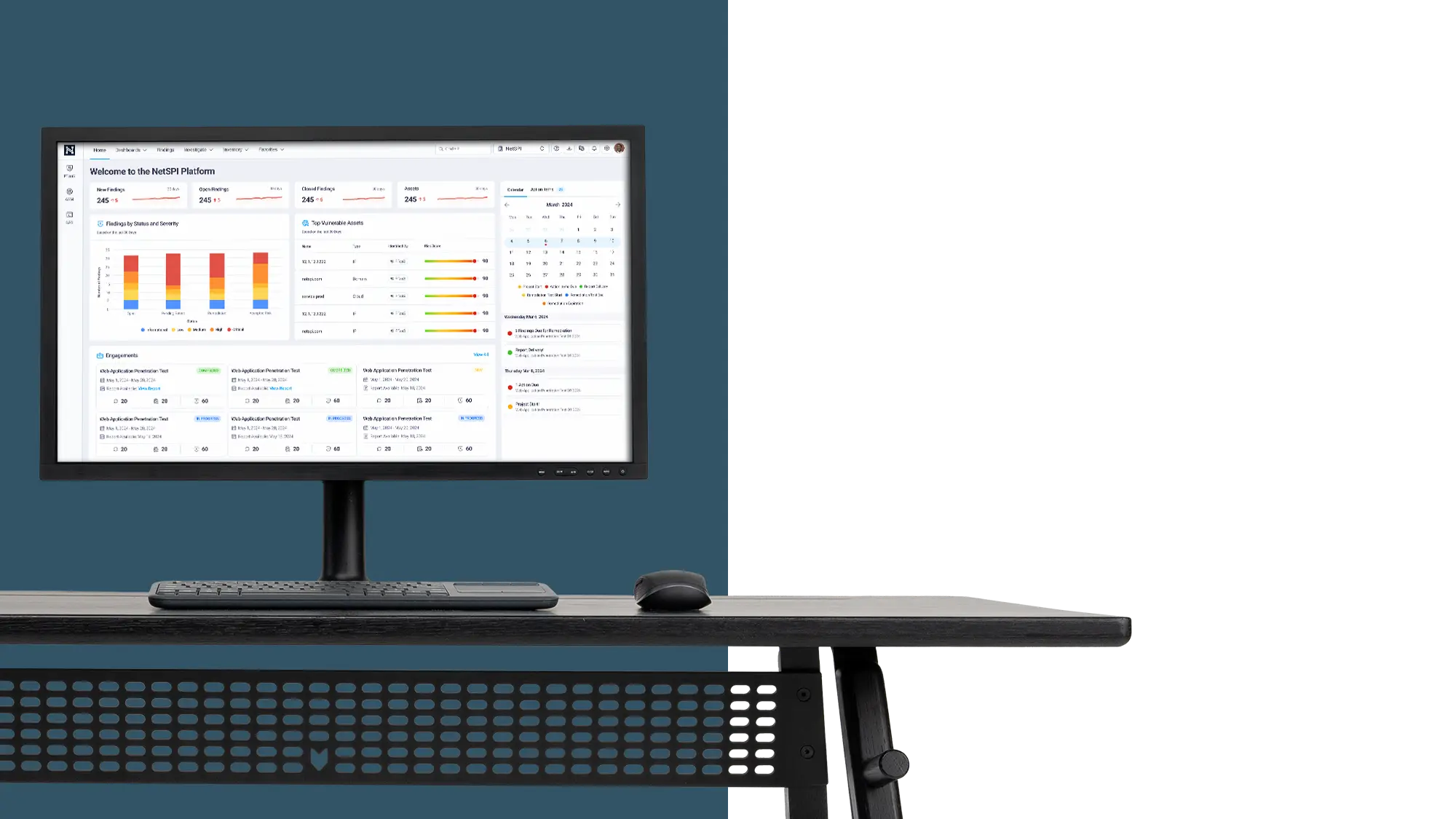
When you pentest with us, you get the value of The NetSPI Platform
NetSPI PTaaS delivers a robust pentesting program that enables you to:
Gain guidance from security experts
Collaborate in real time with our security experts. NetSPI employs more than 250 in-house pentesters that you can trust to deliver consistent, quality manual pentesting results.
Accelerate time to remediation
Live, interactive vulnerability reports make the path to remediation clear and easy. Integrate with your ticketing systems and tools to streamline the remediation process.
Reduce administrative tasks
Spend more time delivering value to your business and less time managing security testing projects. From scoping to remediation, Penetration Testing as a Service removes administrative hassles and makes sure your penetration tests start and end on time.
Improve asset and data fidelity
Contextualize your pentesting data in a single platform with an easy to use and manage asset inventory and get a high-quality inventory of your assets, with high fidelity, manually validated findings so you can have confidence in the results.
Deliver detailed reports
Generate your own PDF reports on-demand. Access fully detailed vulnerability reports as well as executive summaries with high-level results of the engagement. With the NetSPI PtaaS you gain year-round trend analysis and access to dashboards tracking the state of your remediation efforts for all vulnerabilities.

Ebenezer Frimpong
Information Security Analyst at Trella Health
Compare NetSPI PTaaS features
Pentesting features
Usage
Traditional pentesting companies
Usage
Unlimited
Usage
Unlimited
Vulnerabilities
Infinite
Vulnerabilities
Infinite
Integrations
Open API and more than 1,000 integrations including:
- Jira
- Service Now
- Asana
- Microsoft Teams
- Azure Sentinel
- GitHub
- Hubspot
- Amazon SQS
Integrations
Open API and more than 1,000 integrations including:
- Jira
- Service Now
- Asana
- Microsoft Teams
- Azure Sentinel
- GitHub
- Hubspot
- Amazon SQS
Scanning
Traditional pentesting companies
Continuous network testing

Continuous network testing

Continuous web application testing

Continuous web application testing

Vulnerability management
Traditional pentesting companies
Live vulnerability reporting

Live vulnerability reporting

Unlimited vulnerability hosting

Unlimited vulnerability hosting

Vulnerability deduplication

Vulnerability deduplication

Risk scoring

Risk scoring

Custom severities

Custom severities

User assignments

User assignments

Custom remediation SLAs

Custom remediation SLAs

Program management
Traditional pentesting companies
Dedicated project manager


Dedicated project manager


Self-service pentest scoping

Self-service pentest scoping

Program management dashboard

Program management dashboard

Client Relationship Management

Client Relationship Management

Security testing
Traditional pentesting companies
Manual verification of findings


Manual verification of findings


Asset discovery


Asset discovery


Direct access to NetSPI security experts

Direct access to NetSPI security experts

Obtain findings and results in real-time

Obtain findings and results in real-time

Delivery & remediation
Traditional pentesting companies
PDF/CSV report


PDF/CSV report


Annual NetSPI Platform access

Annual NetSPI Platform access

Integrate seamlessly
NetSPI PTaaS includes 1000+ integrations and an open API to integrate with your existing workflows and save countless hours of manual effort.
- Jira
- Service Now
- Asana
- Microsoft Teams
- and more
Work with the A Team every time
With 250+ in-house security experts, NetSPI operates as a true extension of your team. Our proven methodology and consistent processes ensure you get the A Team, every time. Get the opportunity to work directly with the foremost experts across domains, spanning from mainframes to AI.
You deserve The NetSPI Advantage

Security experts
- 250+ pentesters
- Employed, not outsourced
- Domain expertise

Intelligent process
- Programmatic approach
- Strategic guidance
- Delivery management team

Advanced technology
- Consistent quality
- Deep visibility
- Transparent results




