ESPKey + Long Range RFID Reader = A New Tastic Thief

There have been plenty of blog posts, and security conference talks about building long-range RFID badge readers. Bishop Fox (RFID Hacking Tools) and Inguardians (Make your tastic fun tastic) both have great material on this subject. We’re not going to document how to build another RFID Tastic-Thief. Instead, we’ve come up with a different approach to building a long-range reader that we think is worth sharing.
First of all, check out the ESPKey if you haven’t already. It is available at Red Team Tools. It is one of the best RFID tools you’re not using for physical security assessments. Designed by Octosavvi, the ESPKey is about the size of a postage stamp and crimps onto the Power, Neutral, and Wiegand data wires on the internals of an RFID badge reader. Once installed the device will man-in-the-middle the data transferred from a RFID badge reader to the access control panel. The ESPKey has a wireless access point that when connected to, provides a web interface showing captured badge data, and with the click of a button can replay the captured badge data. A full breakdown of the ESPKey can be found here. Note, that installing the ESPKey on production hardware can be slightly destructive and done improperly may require the re-termination of wires to the badge reader.
(“ESPKey Wiegand Interception Tool.” Red Team Tools, Red Team Tools, redteamtools.com/image/cache/catalog/products/ESPKey/ESPKey3-1000×1000.png.)
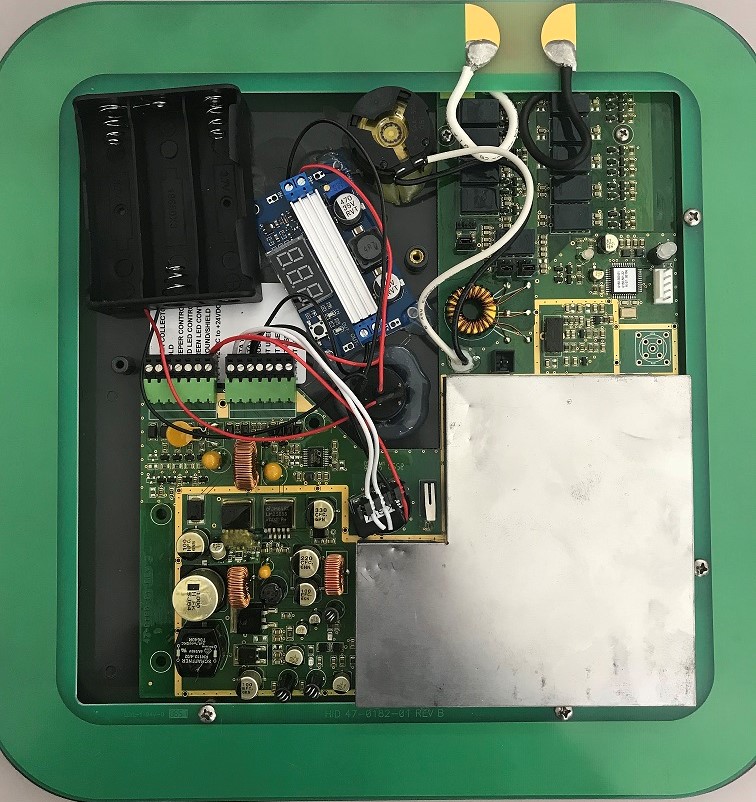
Much like installing the device to capture badge data from an RFID reader mounted on a wall, the ESPKey can also be installed in a portable tastic-style long-range badge reader. The overall advantage of this design is accessing badge data using the ESPKey’s web interface rather than retrieving the data from an SD card. Also, because it intercepts the Wiegand data, it’s hardware agnostic…meaning the design can be used on low and high-frequency long-range readers. It’s also a much simpler setup and install process. We can’t take credit for the overall design. That goes to the The Core Group, who has demoed a similar setup at their SANS training. Below are our lessons learned from the build-out.
Parts Needed
- HID MaxiProx 5375 125kHz Long Range Proximity Reader 5375AGN00
- DROK LM2596 Numerical Control Voltage Switching Regulator DC Buck Converter with Red LED Voltmeter 32V to 24V to 12V to 5V
- DROK DC-DC Boost Voltage Converter, 6A 100W Step Up Regulator Module DC 3-35V to DC 3.5V-35V Adjustable Low Volt Power Supply Transformer Controller Board with LED Display
- ESPKey
- Rocker Switch
- 3 x 18650 case
Schematic
Note, we are not electrical engineers! That should be really obvious based on our schematic below. However, this should be enough detail to build your own low-frequency long range badge reader. Hopefully the diagram is self explanatory. The letters show what and where wires are being connected and terminated.
The reason for this design is to power the reader to 24-volts. Since we are only using 3 x 18650 batteries we need to use a step-up converter to increase the output from 11-volts. The next challenge was to step-down the power for the ESPKey since the device can only handle 9 to 18-volts.
The above example covers incorporating the ESPKey into a low-frequency reader, but a similar design can be used on high-frequency readers as well. Below is a picture of an iClass high-frequency reader with an ESPKey and step-up converter. If the default encryption keys are used, this design makes cloning high-frequency cards a snap.
And there you go! We have used the device on several physical penetration tests with great success! In many cases, we’re able to read badge data 3+ feet away. There are likely other ways to improve these build-outs. We’re not electrical engineers, so any feedback and/or other ideas for RFID testing are welcome!
Explore More Blog Posts

Emulating & Exploiting UEFI: Unveiling Vulnerabilities in Firmware Security
Explore the intricacies of UEFI security with exploration into emulation, dynamic analysis, and the LogoFail vulnerability. Learn how subtle input manipulations can expose critical firmware weaknesses.

Scaling Security with Modern PTaaS: Gartner Report Insights
Discover Gartner® 2025 insights on how PTaaS scales security with continuous validation, automation, and real-time remediation, and how NetSPI can help.

Why Continuous Testing is the New Standard for Modern Security
NetSPI's continuous pentesting delivers regular, tailored assessments across critical assets, customized to your organization's risk profile and operational cadence to ensure coverage where it matters most. These services are delivered through NetSPI’s leading PTaaS platform using existing workflows.