Leading Financial Institution Leveraged NetSPI Red Team Service to Improve Their Security Posture
The Situation
In a report published by consulting firm West Monroe Partners, 40 percent of acquiring businesses said they discovered a high-risk security problem at an acquisition after a deal went through. With this in mind, executive management at one of America’s largest banks wanted to ensure that one of their subsidiaries wasn’t suffering from similar security control gaps. In addition, the bank wanted to understand if identified security gaps could be leveraged to gain unauthorized access to the subsidiary’s networks and resources. To answer those questions, and report on the subsidiary’s responsiveness to real-life attack scenarios, the bank hired NetSPI to conduct a red team operation.
The Approach
During some red team operations, clients provide information to save time, such as employee names, reporting structures, policy details, or system targets. In this instance, the test was conducted using a black box approach, meaning no information was provided by the client. Despite this handicap, NetSPI would put the bank’s newly merged digital infrastructure to the test by attempting to achieve and maintain unauthorized network access via both technical testing methods and social engineering. The bank wanted to know if system, services, or employee identification processes were vulnerable. If so, they wanted NetSPI to exploit those vulnerabilities in order to gain access to critical resources owned by the subsidiary. They also wanted to know if any operating systems or applications were creating immediate risk and if the security controls that were deployed could be bypassed? NetSPI would find out.
The team began by conducting a significant amount of reconnaissance, learning the names of some employees and identifying their email addresses and phone numbers. Armed with this information, NetSPI initiated a targeted social engineering attack. A robo-caller was used to spoof the bank’s voice mail system, asking a targeted employee to verify their identity with their username and password. This tactic was successful in gaining an employee’s username and password. Having successfully obtained the necessary credentials, the next step was to impersonate the employee in an attempt to obtain access to the corporate Virtual Private Network (VPN).
At A Glance
Client
One of the largest U.S. financial institutions offering a comprehensive range of financial services nationwide.
Challenge
Conduct a black box red team assessment to identify weaknesses in network security, policies and procedures.
Approach
Using social engineering and technical testing methods to gain credentials, access the network and escalate privileges.
Results
Security practices and procedures have been strengthened, significantly improving the bank’s overall security posture.
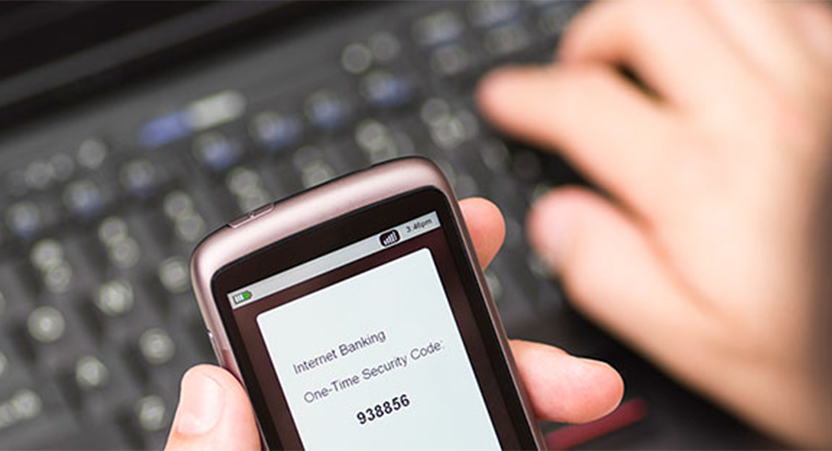
A NetSPI red team member, acting as the targeted employee, called the bank’s IT help desk and stated they were having trouble connecting to corporate network over the VPN. The help desk provided the NetSPI team member with the information below without verifying the caller’s identity beyond asking for their username, which had been obtained using the robo-caller:
- A link where the VPN client could be downloaded.
- Installation instructions for the VPN client
- A one-time token that could be used for the VPN Multi-Factor Authentication (MFA) process, which was sent to a non-corporate email address controlled by the NetSPI red team member.
Now, with remote access to the target network and Active Directory domain credentials in hand, NetSPI started examining the environment for privilege escalation paths. It wasn’t long before a critical discovery was made: a Microsoft Windows server had been left unpatched, enabling the team to exploit the EternalBlue vulnerability. NetSPI then exploited this vulnerability to gain a foothold on the domain system and continue escalation towards establish targets. This foot hold was maintained for multiple days, and the MFA token used to access the network over VPN was reused multiple times. This shined some light on a gap between the bank’s policy that mandates a one-time VPN token to expire after 24 hours and the reality of the subsidiaries implementation.
After multiple days, the bank’s internal IT staff identified that there was an unauthorized user on the network and their Incident Response team was dispatched to confiscate the targeted employee’s compromised laptop. At this point, the bank personnel in the know, revealed to all necessary parties that the bank had engaged NetSPI to conduct a red team assessment. A conference call was quickly held to begin the deconfliction process to ensure that the bank had indeed discovered NetSPI’s activities and not that of an actual attacker. The bank and NetSPI were able to confirm that the red team breach had been discovered. The bank elected to end the engagement and NetSPI moved on to the reporting phase which resulted in a deliverable that contained both the overall narrative of the engagement as well as detailed writeups for all discovered vulnerabilities and weaknesses.
The Results
After the deconfliction process, internal teams worked with NetSPI to understand the attack path and technical testing leveraged throughout the engagement. The bank then took this information and built a remediation plan to address the deficiencies. For example, the off-the-shelf network detection software the bank had installed performed poorly, even though evidence of a network intrusion was captured in the log files. Because the software had not been properly tuned to the environment, alarms were not being triggered even though intrusion had been detected. This has now been remedied along with large improvements to their vulnerability management practices.
In addition, the findings of the assessment resulted in additional funding being made available to address the problem areas highlighted in the final report. A special focus was made on security awareness training for employees, adherence to employee identification and verification practices used by the help desk staff to make them more aware of malicious actors.
To verify the remediation activities were successful at the bank, NetSPI performed additional round of technical testing to verify the identified vulnerabilities were remediated.