NetSPI Recognized for Second Consecutive Year by GigaOm

We’re proud to announce that NetSPI has been recognized in the GigaOm Radar Report for Attack Surface Management. This marks our second consecutive year earning this recognition. This reinforces what our clients already know: NetSPI delivers ASM capabilities designed to reduce risk and drive measurable security outcomes.
For organizations with growing digital ecosystems, attack surface management is no longer optional. Regulatory pressure, ransomware threats, and increasingly complex supply chains require real-time visibility into internet-facing assets. Cybersecurity leaders must know what assets exist, how they are exposed, and which weaknesses present the greatest risk to the business. Being recognized for a second year reflects our commitment to helping our clients proactively identify, prioritize, and remediate attack surface threats for both internal and external assets before attackers can exploit them.
Understanding the GigaOm Radar Report
The GigaOm Radar Report for Attack Surface Management (ASM) evaluates 32 vendors on their ability to provide comprehensive ASM capabilities across key decision criteria, including asset discovery, risk prioritization, workflow integration, and managed services. The report assesses technical and business value, highlighting vendors who demonstrate strong execution, innovation, and customer impact.
The GigaOm Radar Report for ASM provides a clear framework for evaluating vendors in this space, helping decision makers identify providers that can support their needs.
Check out the complete
GigaOm ASM report here.
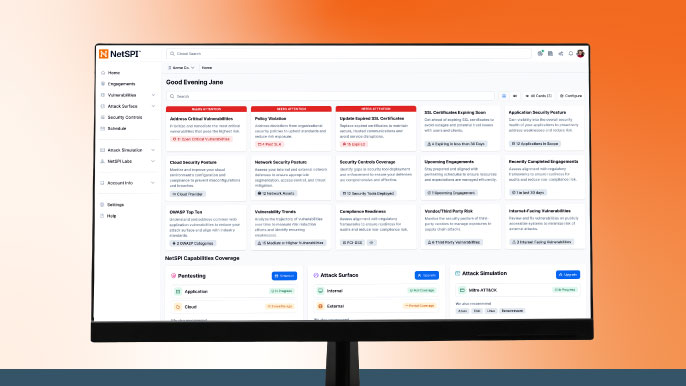
NetSPI Provides 360° Attack Surface Visibility
From cloud workloads to countless web assets, today’s sprawling attack surface creates blind spots that threat actors can exploit. Maintaining a complete, always-on view is no longer optional, it’s essential. That’s why NetSPI delivers 360-degree visibility of your entire attack surface, both internal and external. Our innovative attack surface management capabilities ensure our clients can focus resources on the risks that matter most.
These capabilities include:
- Cloud security configuration scans:
NetSPI provides automated weekly cloud security scans of AWS and Azure environments to identify insecure settings and configurations that could lead to widespread compromise. - Dark web monitoring:
NetSPI enables security teams to proactively detect, investigate, and remediate potential security incidents involving exposed credentials, sensitive information, and organizational mentions. This delivers actionable insights on threats that exist beyond the edge of the environments you control.
- Look-alike Domain monitoring:
NetSPI helps organizations detect registered and unregistered look-alike domains, web addresses that resemble a company’s legitimate domain and are often used in brand impersonation, fraud, phishing, or malware campaigns. - Continuous external asset discovery:
NetSPI conducts weekly discovery scans to monitor your external facing assets and exposures. These results are continuously updated within our Platform to deliver real-time insights on emerging threats across your attack surface.
NetSPI Goes Beyond ASM as a Leader in Modern Pentesting
We’re recognized as a Leader and Outperformer in GigaOm’s Radar Report for Penetration Testing as a Service (PTaaS). The NetSPI Platform unifies attack surface management with comprehensive, proactive pentesting capabilities because we understand that complete attack surface visibility is foundational to an effective penetration testing program. Without knowing what assets exist, even the best pentesting engagement can miss critical exposures.
We believe you shouldn’t have to choose between ASM and pentesting. That’s why we provide our industry-leading attack surface capabilities at no additional cost with every pentesting service.
Our ASM innovation is only part of a broader commitment to modern security programs.
For more details on how we can support your overall security strategy: GigaOm Radar Report for PTaaS
Lets Get Started
Explore More Blog Posts

LiteLLM Supply Chain Compromise
A supply chain attack compromised LiteLLM versions 1.82.7 and 1.82.8 on PyPI, exfiltrating credentials and secrets to an attacker-controlled server.
Meet NetSPI’s Modern Pentesting Experience: Use Case-Driven, AI-Accelerated
The new NetSPI experience represents the next evolution of pentesting—smarter, faster, and designed for scale.
Forrester Recognizes NetSPI in Proactive Security Landscape Report
NetSPI has been recognized among Notable Vendors in the Forrester Proactive Security Platforms Landscape, Q1 2026. Learn how we unify ASM, VRM, and pentesting.

