Beautifying JSON in Burp

Most penetration testers know the pain of trying to view and modify an unparsed JSON string. For those that don’t, here’s a taste:
{"userId":1234,"username":"JakeReynolds","favorites":["Rubik's cubes","Doctor Who"],"dislikes":["Sushi","Vegetables"]}
When looking at thousands of these strings a day it is important for them to be well formatted and easily understandable. There currently exists a Burp Extension for beautifying JSON but it is written in Python, which requires Jython to be downloaded and added to Burp. There were also some issues with Jython and that extension not being as dependable as hoped. Due to those reasons we ported that functionality to Java which is run natively by Burp.
Java makes this extension one-click install, with support from Google’s GSON parser. The source code can be found on our Github as well as PortSwigger’s Github which includes updated build instructions.
To install, simply go to Burp > Extender > BApp Store and select “JSON Beautifier”. The next time there is a JSON request in any of the Burp tabs there will be the option of “JSON Beautifier”. Any content modified in this tab will also be modified in the “Raw” tab. An example is below:
Thanks for checking out our Burp Extension! If you would like any features added feel free to create an issue on Github.
Explore More Blog Posts

LiteLLM Supply Chain Compromise
A supply chain attack compromised LiteLLM versions 1.82.7 and 1.82.8 on PyPI, exfiltrating credentials and secrets to an attacker-controlled server.
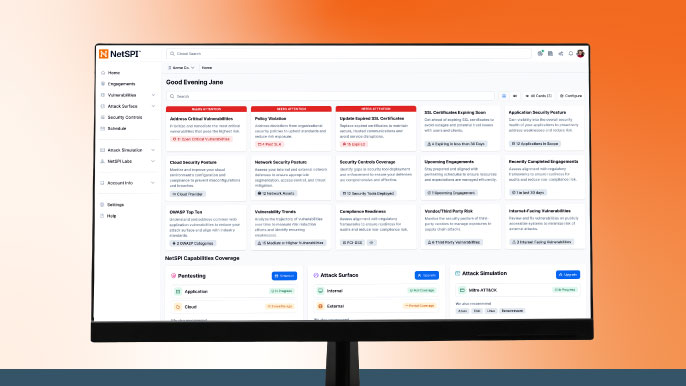
Meet NetSPI’s Modern Pentesting Experience: Use Case-Driven, AI-Accelerated
The new NetSPI experience represents the next evolution of pentesting—smarter, faster, and designed for scale.
Forrester Recognizes NetSPI in Proactive Security Landscape Report
NetSPI has been recognized among Notable Vendors in the Forrester Proactive Security Platforms Landscape, Q1 2026. Learn how we unify ASM, VRM, and pentesting.