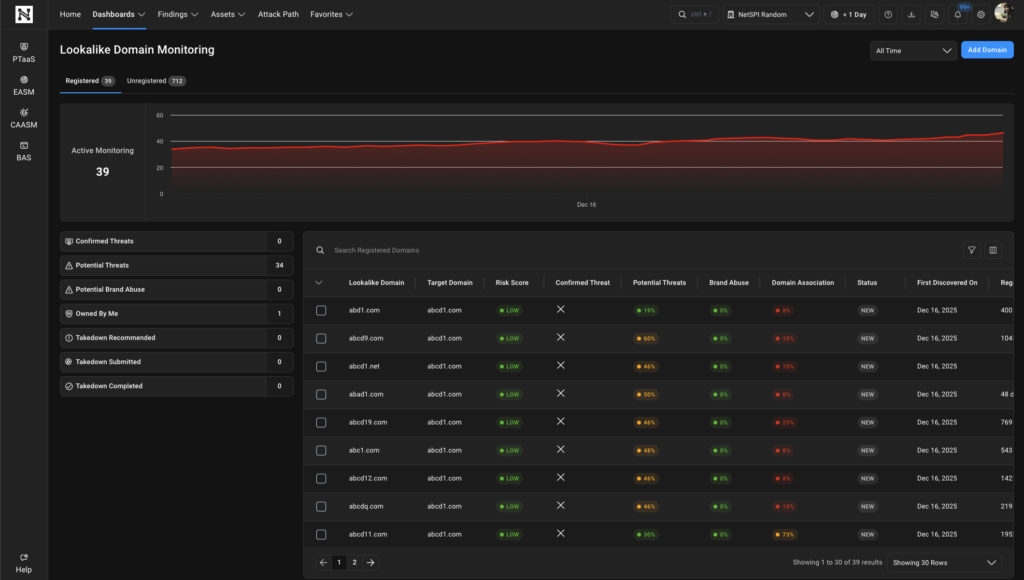
Domain Monitoring
NetSPI’s Domain Monitoring helps organizations identify look-alike domains that resemble their legitimate domains but are be used by attackers for brand impersonation, fraud, phishing, or malware campaigns. This innovation is included on our platform with your pentesting services.
Monitor Look-alike Domains
Domain Monitoring Services help organizations detect registered and unregistered look-alike domains, web addresses that resemble a company’s legitimate domain. These type of look-alike domains are often used in fraudulent activity such as brand impersonation, phishing, or malware campaigns. Attackers create these domains by making subtle modifications to real domain names that are difficult to spot at first glance.
Key Features:
-
Potential Threat Score
-
Confirmed Threat Score
-
Brand Abuse Score
-
Domain Association
-
Takedown Reports
-
Proactive Acquisition
“”

Common Attacker Use Cases
-
Phishing Campaigns
-
Credential Harvesting
-
Malware Distribution
-
Brand Impersonation
-
Command & Control
-
Social Engineering
“”


 Scott Sutherland
Scott Sutherland