EPISODE 028 – Is Data Science the Key to a Mature Security Program?
Episode Details:
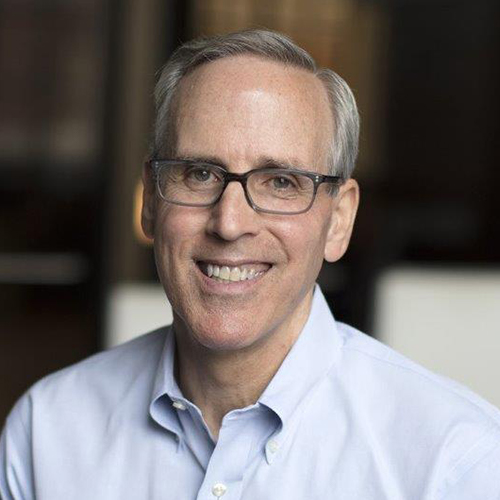
In this episode of Agent of Influence, Nabil speaks with Jim Routh, a well-known security leader and current board member at various innovative early-stage cybersecurity startups. Listen to Jim’s insights on how to define and encourage innovation, build a mature security program using data science, why risk frameworks alone are not enough, security past versus security present, how the pandemic has challenged the human factor, and last but not least, his pickleball hobby.
Explore More Podcasts
EPISODE 05 – Proactive Cloud Security: Mitigate Real Risks
In this episode of the Hack Responsibly podcast, NetSPI VP of Research Karl Fosaaen connects with Thomas Elling, Director of Cloud Penetration Testing.

EPISODE 04 – From Blue Team to Pentesting: Tools, Tales, and Techniques
In this episode, host Karl Fosaaen sits down with Paul Ryan, Senior Director of Application Security at NetSPI, to explore his journey in cybersecurity and his leadership in application pentesting. Paul shares how his career evolved from IT and blue team roles to becoming a key figure in application security at NetSPI.

EPISODE 03 – The Hidden Risk in Legacy Infrastructure
In this episode of the Hack Responsibly podcast, NetSPI VP of Research Karl Fosaaen connects with Phil Young, NetSPI Director of Mainframe Pentesting. Known in the industry as "Soldier of Fortran," Phil is a leading authority on mainframe security.